|
A recent House hearing on the protection of journalistic sources veered into startling territory.
As expected, celebrated investigative journalist Catherine Herridge spoke movingly about her facing potential fines of up to $800 a day and a possible lengthy jail sentence as she faces a contempt charge for refusing to reveal a source in court. Herridge said one of her children asked, “if I would go to jail, if we would lose our house, and if we would lose our family savings to protect my reporting source.” Herridge later said that CBS News’ seizure of her journalistic notes after laying her off felt like a form of “journalistic rape.” Witnesses and most members of the House Judiciary subcommittee on the Constitution and Limited Government agreed that the Senate needs to act on the recent passage of the bipartisan Protect Reporters from Exploitative State Spying (PRESS) Act. This bill would prevent federal prosecutors from forcing journalists to burn their sources, as well to bar officials from surveilling phone and email providers to find out who is talking to journalists. Sharyl Attkisson, like Herridge a former CBS News investigative reporter, brought a dose of reality to the proceeding, noting that passing the PRESS Act is just the start of what is needed to protect a free press. “Our intelligence agencies have been working hand in hand with the telecommunications firms for decades, with billions of dollars in dark contracts and secretive arrangements,” Attkisson said. “They don’t need to ask the telecommunications firms for permission to access journalists’ records, or those of Congress or regular citizens.” Attkisson recounted that 11 years ago CBS News officially announced that Attkisson’s work computer had been targeted by an unauthorized intrusion. “Subsequent forensics unearthed government-controlled IP addresses used in the intrusions, and proved that not only did the guilty parties monitor my work in real time, they also accessed my Fast and Furious files, got into the larger CBS system, planted classified documents deep in my operating system, and were able to listen in on conversations by activating Skype audio,” Attkisson said. If true, why would the federal government plant classified documents in the operating system of a news organization unless it planned to frame journalists for a crime? Attkisson went to court, but a journalist – or any citizen – has a high hill to climb to pursue an action against the federal government. Attkisson spoke of the many challenges in pursuing a lawsuit against the Department of Justice. “I’ve learned that wrongdoers in the federal government have their own shield laws that protect them from accountability,” Attkisson said. “Government officials have broad immunity from lawsuits like mine under a law that I don’t believe was intended to protect criminal acts and wrongdoing but has been twisted into that very purpose. “The forensic proof and admission of the government’s involvement isn’t enough,” she said. “The courts require the person who was spied on to somehow produce all the evidence of who did what – prior to getting discovery. But discovery is needed to get more evidence. It’s a vicious loop that ensures many plaintiffs can’t progress their case even with solid proof of the offense.” Worse, Attkisson testified that a journalist “who was spied on has to get permission from the government agencies involved in order to question the guilty agents or those with information, or to access documents. It’s like telling an assault victim that he has to somehow get the attacker’s permission in order to obtain evidence. Obviously, the attacker simply says no. So does the government.” This hearing demonstrated how important Fourth Amendment protections against unreasonable searches and seizures are to the First Amendment’s guarantee of freedom of the press. If Attkisson’s claims are true, the government explicitly violated a number of laws, not the least of which is mishandling classified documents and various cybercrimes. And it relies on specious immunities and privileges to avoid any accountability for its apparent crimes. Two proposed laws are a good way to start reining in such government misconduct. The first is the PRESS Act, which would protect journalists’ sources against being pressured by prosecutors in federal court to reveal their sources. The second proposed law is the Fourth Amendment Is Not For Sale Act, which passed the House last week. This bill would require the government to get a warrant before it can inspect our personal, digital information sold by data brokers. And, of course, these and other laws limiting government misconduct need genuine remedies and consequences for misconduct, not the mirage of remedies enfeebled by improper immunities. Five Maine lobstermen are suing Maine’s Department of Marine Resources after the agency issued regulations requiring electronic tracking of vessels fishing in federal waters. The plaintiffs allege such tracking violates privacy rights, due process, and equal protection under the Constitution. It’s a red-hot, lobster pot controversy with significant implications on the ever-evolving body of law surrounding geolocation tracking and surveillance.
Maine adopted the tracking regulation in December to comply with a requirement issued by the Atlantic States Marine Fisheries Commission, whose overarching policy objective here is to help protect the North Atlantic right whale. This is certainly a noble objective, but it brings with it troubling implications. Maine Department of Marine Resources Commissioner Patrick Keliher makes the argument that because lobstermen work in a “closely regulated industry,” they have “a greatly reduced expectation of privacy.” It’s a common refrain for those seeking to impose new surveillance measures. But as attorney John Vecchione of the New Civil Liberties Alliance once said, “the expansion of closely regulated-industry theory is a huge, huge danger to liberties for everybody.” Indeed, as society, the economy, and ensuing regulations grow, simply having to get a license could subject any business to warrantless inspections. Such an argument could be used to attach trackers to realtors as they move around from house to house, salespersons, contractors, or any other group of mobile professionals. The U.S. District Court for the District of Maine, where the case was filed, might take a page from the Fifth Circuit, which in 2023 struck down a U.S. Department of Commerce requirement that would have forced charter boat owners to install, at their own expense, a “vessel monitoring system” that would continuously transmit their boats’ location, regardless of whether it was being used for commercial or personal purposes. In that case, the court found that it “borders on incredible” that the government claimed it failed to notice personal privacy concerns in public comments to its rule. The court, further, found that discovery of prime fishing spots in the Gulf would constitute a hardship for many charter operators. Similarly, attorneys for the suing lobstermen argue that they “jealously guard the whereabouts and the techniques they use to place their traps. This is directly correlated to their ability to make a living.” It’s not just fishing locations that are at risk, however. The U.S. Supreme Court has repeatedly held that warrantless GPS tracking constitutes an unlawful search. Tracking someone’s movements, it needn’t be emphasized, can reveal quite a lot about their personal and private lives. As the Maine federal court considers these issues, we side unequivocally with the lobstermen. Simply put, there must be a way to balance the privacy interests of fishermen and the policy objective of protecting marine life. Top-down surveillance mandates seem a poor fit. Forbes reports that federal authorities were granted a court order to require Google to hand over the names, addresses, phone numbers, and user activities of internet surfers who were among the more than 30,000 viewers of a post. The government also obtained access to the IP addresses of people who weren’t logged onto the targeted account but did view its video.
The post in question is suspected of being used to promote the sale of bitcoin for cash, which would be a violation of money-laundering rules. The government likely had good reason to investigate that post. But did it have to track everyone who came into contact with it? This is a prime example of the government’s street-sweeper shotgun approach to surveillance. We saw this when law enforcement in Virginia tracked the location histories of everyone in the vicinity of a robbery. A state judge later found that search meant that everyone in the area, from restaurant patrons to residents of a retirement home, had “effectively been tailed.” We saw the government shotgun approach when the FBI secured the records of everyone in the Washington, D.C., area who used their debit or credit cards to make Bank of America ATM withdrawals between Jan. 5 and Jan. 7, 2021. We also saw it when the FBI, searching for possible foreign influence in a congressional campaign, used FISA Section 702 data – meant to surveil foreign threats on foreign soil – to pull the data of 19,000 political donors. Surfing the web is not inherently suspicious. What we watch online is highly personal, potentially revealing all manner of social, romantic, political, and religious beliefs and activities. The Founders had such dragnet-style searches precisely in mind when they crafted the Fourth Amendment. Simply watching a publicly posted video is not by itself probable cause for search. It should not compromise one’s Fourth Amendment rights. Byron Tau – journalist and author of Means of Control, How the Hidden Alliance of Tech and Government Is Creating a New American Surveillance State – discusses the details of his investigative reporting with Liza Goitein, senior director of the Brennan Center for Justice's Liberty & National Security Program, and Gene Schaerr, general counsel of the Project for Privacy and Surveillance Accountability.
Byron explains what he has learned about the shadowy world of government surveillance, including how federal agencies purchase Americans’ most personal and sensitive information from shadowy data brokers. He then asks Liza and Gene about reform proposals now before Congress in the FISA Section 702 debate, and how they would rein in these practices. Just as the government hates encryption, so too does it hate encryption’s physical analogue in the form of safety deposit boxes.
The mere existence of US Private Vaults – a company in Beverly Hills that could not reveal customers’ names because it did not collect them and could not open the vaults it provided because it did not keep duplicate keys – was prima facie evidence to the FBI of wrongdoing. Seeking to expose what it believed would be a nest of drug dealer cash, the FBI persuaded a magistrate to allow agents to open these vaults with the express purpose of checking the identities of account holders on sheets taped to the inside of the vault’s safety deposit boxes. FBI agents took this warrant as an excuse to seize assets over $5,000 – though the owners were charged with no crime. In 2021, Reason documented in stills taken from surveillance footage how agents rampaged through the vaults and boxes in a frenzy, ripping open a heavy-duty envelope full of gold coins kept by an 80-year-old woman for her retirement savings. Coins fell to the floor, which the FBI cannot account for now. Some $2,000 in cash seemingly “disappeared.” The woman and other victims, with the help of the Institute for Justice, mounted a class-action lawsuit against the FBI. While US Private Vaults later pled guilty to money laundering charges, these plaintiffs had a host of mundane reasons for turning to its services. Reasons varied from distrust of the stability of banks during the Covid era, to transferring assets from a bank in a wildfire zone, to finding that safety deposit boxes at other institutions had long waiting lists. The Ninth Circuit unanimously reversed a lower court verdict and rebuked the FBI for a lawless search. Judge Milan Smith Jr. said the government had opened the door to the “limitless searches of an individual’s personal belongings” reminiscent of the agents of the British crown in ransacking colonial America. The Ninth’s strong stand for the Fourth Amendment is good news. But, as we have seen in governments’ war on encryption, there is a mindset shared by many in law enforcement that something private is inherently suspicious and worthy of warrantless examination. The reform coalition on Capitol Hill remains determined to add strong amendments to Section 702 of the Foreign Intelligence Surveillance Act (FISA). But will they get the chance before an April 19th deadline for FISA Section 702’s reauthorization?
There are several possible scenarios as this deadline closes. One of them might be a vote on the newly introduced “Reforming Intelligence and Securing America” (RISA) Act. This bill is a good-faith effort to represent the narrow band of changes that the pro-reform House Judiciary Committee and the status quo-minded House Permanent Select Committee on Intelligence could agree upon. But is it enough? RISA is deeply lacking because it leaves out two key reforms.
The bill does include a role for amici curiae, specialists in civil liberties who would act as advisors to the secret FISA court. RISA, however, would limit the issues these advisors could address, well short of the intent of the Senate when it voted 77-19 in 2020 to approve the robust amici provisions of the Lee-Leahy amendment. For all these reasons, reformers should see RISA as a floor, not as a ceiling, as the Section 702 showdown approaches. The best solution to the current impasse is to stop denying Members of Congress the opportunity for a straight up-or-down vote on reform amendments. The reauthorization of FISA Section 702, which allows federal agencies to conduct international surveillance for national security purposes, has languished in Congress like an old Spanish galleon caught in the doldrums. This happened after opponents of reform pulled Section 702 reauthorization from the House floor rather than risk losing votes on popular measures, such as requiring government agencies to obtain warrants before surveilling Americans’ communications.
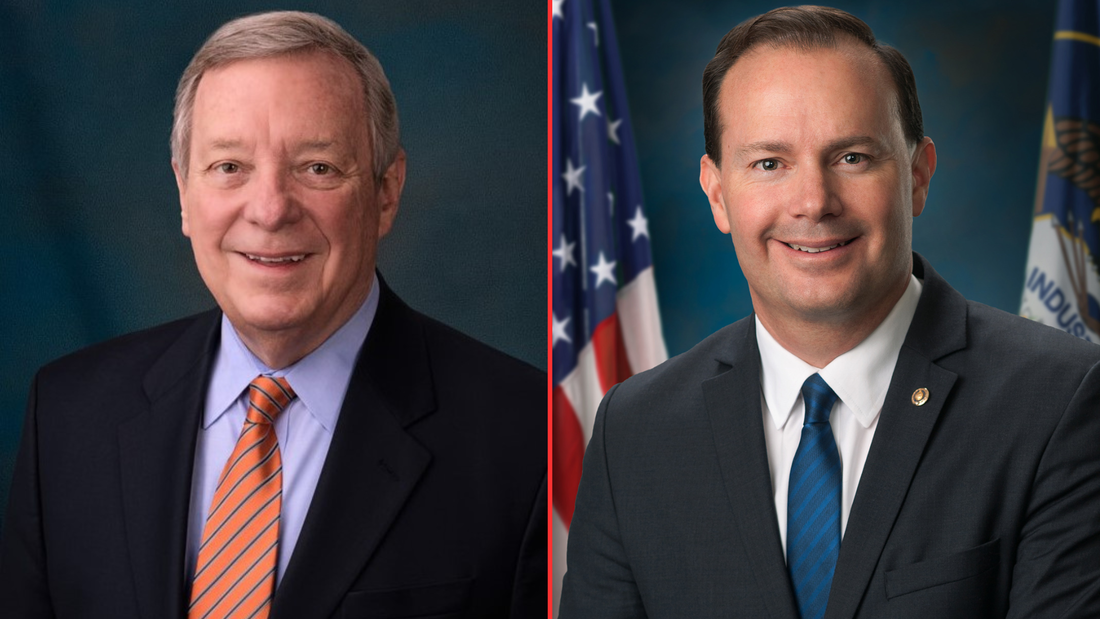
But the winds are no longer becalmed. They are picking up – and coming from the direction of reform. Sen. Dick Durbin (D-IL), Chairman of the Senate Judiciary Committee, and fellow committee member Sen. Mike Lee (R-UT), today introduced the Security and Freedom Enhancement (SAFE) Act. This bill requires the government to obtain warrants or court orders before federal agencies can access Americans’ personal information, whether from Section 702-authorized programs or purchased from data brokers. Enacted by Congress to enable surveillance of foreign targets in foreign lands, Section 702 is used by the FBI and other federal agencies to justify domestic spying. According to the Foreign Intelligence Surveillance Act (FISA) Court, under Section 702 government “batch” searches have included a sitting U.S. Congressman, a U.S. Senator, journalists, political commentators, a state senator, and a state judge who reported civil right violations by a local police chief to the FBI. It has even been used by government agents to stalk online romantic prospects. Millions of Americans in recent years have had their communications compromised by programs under Section 702. The reforms of the SAFE Act promise to reverse this trend, protecting Americans’ privacy and constitutional rights from the government. The SAFE Act requires:
Durbin-Lee is a pragmatic bill. It lifts warrants and other requirements in emergency circumstances. The SAFE Act allows the government to obtain consent for surveillance if the subject of the search is a potential victim or target of a foreign plot. It allows queries designed to identify targets of cyberattacks, where the only content accessed and reviewed is malicious software or cybersecurity threat signatures. The SAFE Act is a good-faith effort to strike a balance between national security and Americans’ privacy. It should break the current stalemate, renewing the push for debate and votes on amendments to the reauthorization of Section 702. While Congress debates adding reforms to FISA Section 702 that would curtail the sale of Americans’ private, sensitive digital information to federal agencies, the Federal Trade Commission is already cracking down on companies that sell data, including their sales of “location data to government contractors for national security purposes.”
The FTC’s words follow serious action. In January, the FTC announced proposed settlements with two data aggregators, X-Mode Social and InMarket, for collecting consumers’ precise location data scraped from mobile apps. X-Mode, which can assimilate 10 billion location data points and link them to timestamps and unique persistent identifiers, was targeted by the FTC for selling location data to private government contractors without consumers’ consent. In February, the FTC announced a proposed settlement with Avast, a security software company, that sold “consumers’ granular and re-identifiable browsing information” embedded in Avast’s antivirus software and browsing extensions. What is the legal basis for the FTC’s action? The agency seems to be relying on Section 5 of the Federal Trade Commission Act, which grants the FTC power to investigate and prevent deceptive trade practices. In the case of X-Mode, the FTC’s proposed complaint highlight’s X-Mode’s statement that their location data would be used solely for “ad personalization and location-based analytics.” The FTC alleges X-Mode failed to inform consumers that X-Mode “also sold their location data to government contractors for national security purposes.” The FTC’s evolving doctrine seems even more expansive, weighing the stated purpose of data collection and handling against its actual use. In a recent blog, the FTC declares: “Helping people prepare their taxes does not mean tax preparation services can use a person’s information to advertise, sell, or promote products or services. Similarly, offering people a flashlight app does not mean app developers can collect, use, store, and share people’s precise geolocation information. The law and the FTC have long recognized that a need to handle a person’s information to provide them a requested product or service does not mean that companies are free to collect, keep, use, or share that’s person’s information for any other purpose – like marketing, profiling, or background screening.” What is at stake for consumers? “Browsing and location data paint an intimate picture of a person’s life, including their religious affiliations, health and medical conditions, financial status, and sexual orientation.” If these cases go to court, the tech industry will argue that consumers don’t sign away rights to their private information when they sign up for tax preparation – but we all do that routinely when we accept the terms and conditions of our apps and favorite social media platforms. The FTC’s logic points to the common understanding that our data is collected for the purpose of selling us an ad, not handing over our private information to the FBI, IRS, and other federal agencies. The FTC is edging into the arena of the Fourth Amendment Is Not for Sale Act, which targets government purchases and warrantless inspection of Americans’ personal data. The FTC’s complaints are, for the moment, based on legal theory untested by courts. If Congress attaches similar reforms to the reauthorization of FISA Section 702, it would be a clear and hard to reverse protection of Americans’ privacy and constitutional rights. Ken Blackwell, former ambassador and mayor of Cincinnati, has a conservative resume second to none. He is now a senior fellow of the Family Research Council and chairman of the Conservative Action Project, which organizes elected conservative leaders to act in unison on common goals. So when Blackwell writes an open letter in Breitbart to Speaker Mike Johnson warning him not to try to reauthorize FISA Section 702 in a spending bill – which would terminate all debate about reforms to this surveillance authority – you can be sure that Blackwell was heard.
“The number of FISA searches has skyrocketed with literally hundreds of thousands of warrantless searches per year – many of which involve Americans,” Blackwell wrote. “Even one abuse of a citizen’s constitutional rights must not be tolerated. When that number climbs into the thousands, Congress must step in.” What makes Blackwell’s appeal to Speaker Johnson unique is he went beyond including the reform efforts from conservative stalwarts such as House Judiciary Committee Chairman Jim Jordan and Rep. Andy Biggs of the Freedom Caucus. Blackwell also cited the support from the committee’s Ranking Member, Rep. Jerry Nadler, and Rep. Pramila Jayapal, who heads the House Progressive Caucus. Blackwell wrote: “Liberal groups like the ACLU support reforming FISA, joining forces with conservatives civil rights groups. This reflects a consensus almost unseen on so many other important issues of our day. Speaker Johnson needs to take note of that as he faces pressure from some in the intelligence community and their overseers in Congress, who are calling for reauthorizing this controversial law without major reforms and putting that reauthorization in one of the spending bills that will work its way through Congress this month.” That is sound advice for all Congressional leaders on Section 702, whichever side of the aisle they are on. In December, members of this left-right coalition joined together to pass reform measures out of the House Judiciary Committee by an overwhelming margin of 35 to 2. This reform coalition is wide-ranging, its commitment is deep, and it is not going to allow a legislative maneuver to deny Members their right to a debate. The growth of the surveillance state in Washington, D.C., is coinciding with a renewed determination by federal agencies to expose journalists’ notes and sources. Recent events show how our Fourth Amendment right against unreasonable searches and seizures and our First Amendment right of a free press are inextricable and mutually reinforcing – that if you degrade one of these rights, you threaten both of them.
In May, the FBI raided the home of journalist Tim Burke, seizing his computer, hard drives, and cellphone, after he reported on embarrassing outtakes of a Fox News interview. It turns out these outtakes had already been posted online. Warrants were obtained, but on what credible allegation of probable cause? Or consider CBS News senior correspondent Catherine Herridge who was laid off, then days later ordered by a federal judge to reveal the identity of a confidential source she used for a series of 2017 stories published while she worked at Fox News. Shortly afterwards, Herridge was held in contempt for refusing to divulge that source. This raises the question that when CBS had earlier terminated Herridge and seized her files, would network executives have been willing to put their freedom on the line as Herridge has done? In response to public outcry, CBS relented and handed Herridge’s notes back to her. But local journalists cannot count on generating the national attention and sympathy that a celebrity journalist can. Now add to this vulnerability the reality that every American who is online – whether a national correspondent or a college student – has his or her sensitive and personal information sold to more than a dozen federal agencies by data brokers, a $250 billion industry that markets our data in the shadows. The sellers of our privacy compile nearly limitless data dossiers that “reveal the most intimate details of our lives, our movements, habits, associations, health conditions, and ideologies.” Data brokers have established a sophisticated system to aggregate data from nearly every platform and device that records personal information to develop detailed profiles on individuals. To fill in the blanks, they also sweep up information from public records. So if you have a smartphone, apps, or search online, your life is already an open book to the government. In this way, state and federal intelligence and law enforcement agencies can use the data broker loophole to obtain information about Americans that they would otherwise need a warrant, court order, or subpoena to obtain. Now imagine what might happen as these two trends converge – a government hungry to expose journalists’ sources, but one that also has access to a journalist’s location history, as well as everyone they have called, texted, and emailed. It is hardly paranoid, then, to worry that when a prosecutor tries to compel a journalist to give up a source through legal means, purchased data may have already given the government a road map on what to seek. The combined threat to privacy from pervasive surveillance and prosecutors seeking journalists’ notes is serious and growing. This is why PPSA supports legislation to protect journalistic privacy and close the data broker loophole. The Protect Reporters from Exploitive State Spying, or PRESS Act, would grant a privilege to protect confidential news sources in federal legal proceedings, while offering reasonable exceptions for extreme situations. Such “shield laws” have been put into place in 49 states. The PRESS Act, which passed the House in January with unanimous, bipartisan support, would bring the federal government in line with the states. Likewise, the Fourth Amendment Is Not For Sale Act would close the data broker loophole and require the government to obtain a warrant before it can seize our personal information, as required by the Fourth Amendment of the U.S. Constitution. The House Judiciary Committee voted to advance the Fourth Amendment Is Not For Sale Act out of committee with strong bipartisan support in July. The Judiciary Committee also reported out a strong data broker loophole closure as part of the Protect Liberty Act in December. Now, it’s up to Congress to include these protection and reform measures in the reauthorization of Section 702. PPSA urges lawmakers to pass measures to protect privacy and a free press. They will rise or fall together. When we covered a Michigan couple suing their local government for sending a drone over their property to prove a zoning violation, we asked if there are any legal limits to aerial surveillance of your backyard.
In this case before the Michigan Supreme Court, Maxon v. Long Lake Township, counsel for the local government said that the right to inspect our homes goes all the way to space. He described the imaging capability of Google Earth satellites, asking: “If you want to know whether it’s 50 feet from this house to this barn, or 100 feet from this house to this barn, you do that right on the Google satellite imagery. And so given the reality of the world we live in, how can there be a reasonable expectation of privacy in aerial observations of property?” One justice reacted to the assertion that if Google Earth could map a backyard as closely and intimately as a drone, that would be a search. “Technology is rapidly changing,” the justice responded. “I don’t think it is hard to predict that eventually Google Earth will have that capacity.” Now William J. Broad of The New York Times reports that we’re well beyond Google Earth’s imaging of barns and houses. Try dinner plates and forks. Albedo Space of Denver is making a fleet of 24 small, low orbit satellites that will use imagery to guide responders in disasters, such as wildfires and other public emergencies. It will improve the current commercial standard of satellite imaging from a focal length of about a foot to about four inches. A former CIA official with decades of satellite experience told Broad that it will be a “big deal” when people realize that anything they are trying to hide in their backyards will be visible. Skinny-dipping in the pool will only be for the supremely confident. To his credit, Albedo chief Topher Haddad said, “we’re acutely aware of the privacy implications,” promising that management will be selective in their choice of clients on a case-by-case basis. It is good to know that Albedo likely won’t be using its technology to catch zone violators or backyard sunbathers. We’ve seen, however, that what is cutting-edge technology today will be standard tomorrow. This is just one more way in which the velocity of technology is outpacing our ability to adjust. There is, of course, one effective response. We can reject the Michigan town’s counsel argument who said, essentially, that privacy’s dead and we should just get over it. Courts and Congress should define orbital and aerial surveillance as searches requiring a probable cause warrant, as defined by the Fourth Amendment of the U.S. Constitution, before our homes and backyards can be invaded by eyes from above. The greatest danger to privacy is not that Albedo will allow government snoops to watch us in real time. The real threat is a satellite company’s ability to collect private images by the tens of millions. Such a database could then be sold to the government just as so much commercial digital information is now being sold to the government by data brokers. This is all the more reason for Congress to import the privacy-protecting warrant provisions of the Fourth Amendment Is Not For Sale Act into the reauthorization of FISA Section 702. The word from Capitol Hill is that Speaker Mike Johnson is scheduling a likely House vote on the reauthorization of FISA’s Section 702 this week. We are told that proponents and opponents of surveillance reform will each have an opportunity to vote on amendments to this statute.
It is hard to overstate how important this upcoming vote is for our privacy and the protection of a free society under the law. The outcome may embed warrant requirements in this authority, or it may greatly expand the surveillance powers of the government over the American people. Section 702 enables the U.S. intelligence community to continue to keep a watchful eye on spies, terrorists, and other foreign threats to the American homeland. Every reasonable person wants that, which is why Congress enacted this authority to allow the government to surveil foreign threats in foreign lands. Section 702 authority was never intended to become what it has become: a way to conduct massive domestic surveillance of the American people. Government agencies – with the FBI in the lead – have used this powerful, invasive authority to exploit a backdoor search loophole for millions of warrantless searches of Americans’ data in recent years. In 2021, the secret Foreign Intelligence Surveillance Court revealed that such backdoor searches are used by the FBI to pursue purely domestic crimes. Since then, declassified court opinions and compliance reports reveal that the FBI used Section 702 to examine the data of a House Member, a U.S. Senator, a state judge, journalists, political commentators, 19,000 donors to a political campaign, and to conduct baseless searches of protesters on both the left and the right. NSA agents have used it to investigate prospective and possible romantic partners on dating apps. Any reauthorization of Section 702 must include warrants – with reasonable exceptions for emergency circumstances – before the data of Americans collected under Section 702 or any other search can be queried, as required by the U.S. Constitution. This warrant requirement must include the searching of commercially acquired information, as well as data from Americans’ communications incidentally caught up in the global communications net of Section 702. The FBI, IRS, Department of Homeland Security, the Pentagon, and other agencies routinely buy Americans’ most personal, sensitive information, scraped from our apps and sold to the government by data brokers. This practice is not authorized by any statute, or subject to any judicial review. Including a warrant requirement for commercially acquired information as well as Section 702 data is critical, otherwise the closing of the backdoor search loophole will merely be replaced by the data broker loophole. If the House declines to impose warrants for domestic surveillance, expect many politically targeted groups to have their privacy and constitutional rights compromised. We cannot miss the best chance we’ll have in a generation to protect the Constitution and what remains of Americans’ privacy. Copy and paste the message below and click here to find your U.S. Representative and deliver it: “Please stand up for my privacy and the Fourth Amendment to the U.S. Constitution: Vote to reform FISA’s Section 702 with warrant requirements, both for Section 702 data and for our sensitive, personal information sold to government agencies by data brokers.” Wired reports that police in northern California asked Parabon NanoLabs to run a DNA sample from a cold case murder scene to identify the culprit. Police have often run DNA against the vast database of genealogical tests, cracking cold cases like the Golden State Killer, who murdered at least 13 people.
But what Parabon NanoLabs did for the police in this case was something entirely different. The company produced a 3D rendering of a “predicted face” based on the genetic instructions encoded in the sample’s DNA. The police then ran it against facial recognition software to look for a match. Scientists are skeptical that this is an effective tool given that Parabon’s methods have not been peer-reviewed. Even the company’s director of bioinformatics, Ellen Greytak, told Wired that such face predictions are closer in accuracy to a witness description rather than the exact replica of a face. With the DNA being merely suggestive – Greytak jokes that “my phenotyping can tell you if your suspect has blue eyes, but my genealogist can tell you the guy’s address” – the potential for false positives is enormous. Police multiply that risk when they run a predicted face through the vast database of facial recognition technology (FRT) algorithms, technology that itself is far from perfect. Despite cautionary language from technology producers and instructions from police departments, many detectives persist in mistakenly believing that FRT returns matches. Instead, it produces possible candidate matches arranged in the order of a “similarity score.” FRT is also better with some types of faces than others. It is up to 100 times more likely to misidentify Asian and Black people than white men. The American Civil Liberties Union, in a thorough 35-page comment to the federal government on FRT, biometric technologies, and predictive algorithms, noted that defects in FRT are likely to multiply when police take a low-quality image and try to brighten it, or reduce pixelation, or otherwise enhance the image. We can only imagine the Frankenstein effect of mating a predicted face with FRT. As PPSA previously reported, rights are violated when police take a facial match not as a clue, but as evidence. This is what happened when Porcha Woodruff, a 32-year-old Black woman and nursing student in Detroit, was arrested on her doorstep while her children cried. Eight months pregnant, she was told by police that she had committed recent carjackings and robberies – even though the woman committing the crimes in the images was not visibly pregnant. Woodruff went into contractions while still in jail. In another case, local police executed a warrant by arresting a Georgia man at his home for a crime committed in Louisiana, even though the arrestee had never set foot in Louisiana. The only explanation for such arrests is sheer laziness, stupidity, or both on the part of the police. As ACLU documents, facial recognition forms warn detectives that a match “should only be considered an investigative lead. Further investigation is needed to confirm a match through other investigative corroborated information and/or evidence. INVESTIGATIVE LEAD, NOT PROBABLE CAUSE TO MAKE AN ARREST.” In the arrests made in Detroit and Georgia, police had not performed any of the rudimentary investigative steps that would have immediately revealed that the person they were investigating was innocent. Carjacking and violent robberies are not typically undertaken by women on the verge of giving birth. The potential for replicating error in the courtroom would be multiplied by showing a predicted face to an eyewitness. If a witness is shown a predicted face, that could easily influence the witness’s memory when presented with a line-up. We understand that an investigation might benefit from knowing that DNA reveals that a perp has blue eyes, allowing investigators to rule out all brown- and green-eyed suspects. But a predicted face should not be enough to search through a database of innocent people. In fact, any searches of facial recognition databases should require a warrant. As technology continues to push the boundaries, states need to develop clear procedural guidelines and warrant requirements that protect constituents’ constitutional rights. Late last year, Sen. Ron Wyden (D-OR) put a hold on the appointment of Lt. Gen. Timothy Haugh to replace outgoing National Security Agency director Gen. Paul Nakasone. Late Thursday, Sen. Wyden’s pressure campaign yielded a stark result – a frank admission from Gen. Nakasone that, as long suspected, the NSA purchases Americans’ sensitive, personal online activities from commercial data brokers.
The NSA admitted it buys netflow data, which records connections between computers and servers. Even without the revelation of messages’ contents, such tracking can be extremely personal. A Stanford University study of telephone metadata showed that a person’s calls and texts can reveal connections to sensitive life issues, from Alcoholics Anonymous to abortion clinics, gun stores, mental and health issues including sexually transmitted disease clinics, and connections to faith organizations. Gen. Nakasone’s letter to Sen. Wyden states that NSA works to minimize the collection of such information. He writes that NSA does not buy location information from phones inside the United States, or purchase the voluminous information collected by our increasingly data-hungry automobiles. It would be a mistake, however, to interpret NSA’s internal restrictions too broadly. While NSA is generally the source for signals intelligence for the other agencies, the FBI, IRS, and the Department of Homeland Security are known to make their own data purchases. In 2020, PPSA reported on the Pentagon purchasing data from Muslim dating and prayer apps. In 2021, Sen. Wyden revealed that the Defense Intelligence Agency was purchasing Americans’ location data from our smartphones without a warrant. How much data, and what kinds of data, are purchased by the FBI is not clear. Sen. Wyden did succeed in a hearing last March in prompting FBI Director Christopher Wray to admit that the FBI had, in some period in the recent past, purchased location data from Americans’ smartphones without a warrant. Despite a U.S. Supreme Court opinion, Carpenter (2018), which held that the U.S. Constitution requires a warrant for the government to compel telecom companies to turn over Americans’ location data, federal agencies maintain that the Carpenter standard does not curb their ability to purchase commercially available digital information. In a press statement, Sen. Wyden hammers home the point that a recent Federal Trade Commission order bans X-Mode Social, a data broker, and its successor company, from selling Americans’ location data to government contractors. Another data broker, InMarket Media, must notify customers before it can sell their precise location data to the government. We now have to ask: was Wednesday’s revelation that the Biden Administration is drafting rules to prevent the sale of Americans’ data to hostile foreign governments an attempt by the administration to partly get ahead of a breaking story? For Americans concerned about privacy, the stakes are high. “Geolocation data can reveal not just where a person lives and whom they spend time with but also, for example, which medical treatments they seek and where they worship,” FTC Chair Lina Khan said in a statement. “The FTC’s action against X-Mode makes clear that businesses do not have free license to market and sell Americans’ sensitive location data. By securing a first-ever ban on the use and sale of sensitive location data, the FTC is continuing its critical work to protect Americans from intrusive data brokers and unchecked corporate surveillance.” As Sen. Wyden’s persistent digging reveals more details about government data purchases, Members of Congress are finding all the more reason to pass the Protect Liberty Act, which enforces the Constitution’s Fourth Amendment warrant requirement when the government inspects Americans’ purchased data. This should also put Members of the Senate and House Intelligence Committees on the spot. They should explain to their colleagues and constituents why they’ve done nothing about government purchases of Americans’ data – and why their bills include exactly nothing to protect Americans’ privacy under the Fourth Amendment. More to come … No sooner did the Protect Liberty and End Warrantless Surveillance Act pass the House Judiciary Committee with overwhelming bipartisan support than the intelligence community began to circulate what Winston Churchill in 1906 politely called “terminological inexactitudes.”
The Protect Liberty Act is a balanced bill that respects the needs of national security while adding a warrant requirement whenever a federal agency inspects the data or communications of an American, as required by the Fourth Amendment. This did not stop defenders of the intelligence community from claiming late last year that Section 702 reforms would harm the ability of the U.S. government to fight fentanyl. This is remarkable, given that the government hasn’t cited a single instance in which warrantless searches of Americans’ communications proved useful in combating the fentanyl trade. Nothing in the bill would stop surveillance of factories in China or cartels in Mexico. If an American does become a suspect in this trafficking, the government can and should seek a probable cause warrant, as is routinely done in domestic law enforcement cases. No sooner did we bat that one away than we heard about fresh terminological inexactitudes. Here are two of the latest bits of disinformation being circulated on Capitol Hill about the Protect Liberty Act. Intelligence Community Myth: Members of Congress are being told that under the Protect Liberty Act, the FBI would be forced to seek warrants from district court judges, who might or might not have security clearances, in order to perform U.S. person queries. Fact: The Protect Liberty Act allows the FBI to conduct U.S. person queries if it has either a warrant from a regular federal court or a probable cause order from the FISA Court, where judges have high-level security clearances. The FBI will determine which type of court order is appropriate in each case. Intelligence Community Myth: Members are being told that under the Protect Liberty Act, terrorists can insulate themselves from surveillance by including a U.S. person in a conversation or email thread. Fact: Under the Protect Liberty Act, the FBI can collect any and all communications of a foreign target, including their communications with U.S. persons. Nothing in the bill prevents an FBI agent from reviewing U.S. person information the agent encounters in the course of reviewing the foreign target’s communications. In other words, if an FBI agent is reading a foreign target’s emails and comes across an email to or from a U.S. person, the FBI agent does not need a warrant to read that email. The bill’s warrant requirement applies in one circumstance only: when an FBI agent runs a query designed to retrieve a U.S. person’s communications or other Fourth Amendment-protected information. That is as it should be under the U.S. Constitution. As we face the renewed debate over Section 702 – which must be reauthorized in the next few months – expect the parade of untruths to continue. As they do, PPSA will be here to call them out. National Rifle Association v. Vullo In this age of “corporate social responsibility,” can a government regulator mount a pressure campaign to persuade businesses to blacklist unpopular speakers and organizations? Would such pressure campaigns force banks, cloud storage companies, and other third parties that hold targeted organizations’ data to compromise their clients’ Fourth as well as their First Amendment rights?
These are just some of the questions PPSA is asking the U.S. Supreme Court to weigh in National Rifle Association v. Vullo. Here's the background on this case: Maria Vullo, then-superintendent of the New York Department of Financial Services, used her regulatory clout over banks and insurance companies in New York to strongarm them into denying financial services to the National Rifle Association. This campaign was waged under an earnest-sounding directive to consider the “reputational risk” of doing business with the NRA and firearms manufacturers. Vullo imposed consent orders on three insurers that they never again provide policies to the NRA. She issued guidance that encouraged financial services firms to “sever ties” with the NRA and to “continue evaluating and managing their risks, including reputational risks” that could arise from their dealings with the NRA or similar gun promotion organizations. “When a regulator known to slap multi-million fines on companies issues ‘guidance,’ it is not taken as a suggestion,” said Gene Schaerr, PPSA general counsel. “It’s sounds more like, ‘nice store you’ve got here, it’d be shame if anything happened to it.’” The U.S. Court of Appeals for the Second Circuit reversed a lower court’s decision that found that Vullo used threats to force the companies she regulates to cut ties with the NRA. The Second Circuit reasoned that: “The general backlash against gun promotion groups and businesses … could (and likely does) directly affect the New York financial markets; as research shows, a business's response to social issues can directly affect its financial stability in this age of enhanced corporate social responsibility.” You don’t have to be an enthusiast of the National Rifle Association to see the problems with the Second Circuit’s reasoning. Aren’t executives of New York’s financial services firms better qualified to determine what does and doesn’t “directly affect financial stability” than a regulator in Albany? How aggressive will government become in using its almost unlimited access to buy or subpoena data of a target organization to get its way? We told the Court: “Even the stability of a single company is not enough; the government cannot override the Bill of Rights to slightly reduce the rate of corporate bankruptcies.” In our brief, PPSA informs the U.S. Supreme Court about the dangers of a nebulous, government-imposed “corporate social responsibility standard.” We write: “Using CSR – a controversial theory positing that taking popular or ‘socially responsible’ stances may increase corporate profits – to justify infringement of First Amendment rights poses a grave threat to all Constitutionally-protected individual rights.” PPSA is reminding the Court that the right to free speech and the right to be protected from government surveillance are intwined. CVS, Kroger, and Rite Aid Hand Over Americans’ Prescriptions Records to Police Upon Request1/17/2024
Three of the largest pharmaceutical chains – CVS Health, Kroger, and Rite Aid – routinely hand over the prescription and medical records of Americans to police and government agencies upon request, no warrant required.
“Americans' prescription records are among the most private information the government can obtain about a person,” Sen. Ron Wyden (D-OR), and Reps. Pramila Jayapal (D-WA) and Sara Jacobs (D-CA) wrote in a letter to HHS Secretary Xavier Becerra revealing the results of a congressional investigation into this practice. “They can reveal extremely personal and sensitive details about a person’s life, including prescriptions for birth control, depression or anxiety medications, or other private medical conditions.” The Washington Post reports that because the chains often share records across all locations, a pharmacy in one state can access a person’s medical history from states with more restrictive laws. Five pharmacies – Amazon, Cigna, Optum Rx, Walmart, and Walgreens Boots Alliance – require demands for pharmacy records by law enforcement to be reviewed by legal professionals. One of them, Amazon, informs consumers of the request unless hit with a gag order. All the major pharmacies will release customer records, however, if they are merely given a subpoena issued by a government agency rather than a warrant issued by a judge. This could be changed by corporate policy. Sen. Wyden and Reps. Jayapal and Jacobs urge pharmacies to insist on a warrant rather than comply with a request or a subpoena. Most Americans are familiar with the strict privacy provisions of the Health Insurance Portability and Accountability Act (HIPAA) from filling out forms in the doctor’s office. Most will surely be surprised how HIPAA, as strict as it is for physicians and hospitals, is wide open for warrantless inspection by the government. This privacy vulnerability is just one more example of the generous access government agencies have to almost all of our information. Intelligence and law enforcement agencies can know just about everything about us through purchases of our most sensitive and personal information reaped by our apps and sold to the government by data brokers. As privacy champions in Congress press HHS to revise its HIPAA regulations to protect Americans’ medical data from warrantless inspection, Congress should also close all the loopholes by passing the Protect Liberty and End Warrantless Surveillance Act. The Federal Reserve Board is publicly weighing whether or not to ask Congress to allow it to establish a Central Bank Digital Currency (CBDC), replacing paper dollars with government-issued electrons.
Given the growth of computing, a digital national currency may seem inevitable. But it would be a risky proposition from the standpoint of cybersecurity, national security, and unintended consequences for the economy. A CBDC would certainly pose a significant threat to Americans’ privacy. A factsheet on the Federal Reserve website says, “Any CBDC would need to strike an appropriate balance between safeguarding the privacy rights of consumers and affording the transparency necessary to deter criminal activity.” The Fed imagines that such a scheme would rely on privacy-sector intermediaries to create digital wallets and protect consumers’ privacy. Given the hunger that officialdom in Washington, D.C., has shown for pulling in all our financial information – including a serious proposal to record transactions from bank accounts, digital wallets, and apps – the Fed’s balancing of our privacy against surveillance of the currency is troubling. With digital money, government would have in its hands the ability to surveil all transactions, tracing every dollar from recipient to spender. Armed with such power, the government could debank any number of disfavored groups or individuals. If this sounds implausible, consider that debanking was exactly the strategy the Canadian government used against the trucker protestors two years ago. Enter H.R. 1122 – the CBDC Anti-Surveillance State Act – which sets down requirements for a digital currency. This bill would prohibit the Federal Reserve from using CBDC to implement monetary policy. It would require the Fed to report the results of a study or pilot program to Congress on a quarterly basis and consult with the brain trust of the Fed’s regional banks. Though this bill prevents the Fed from issuing CBDC accounts to individuals directly, there is a potential loophole in this bill – the Fed might still maintain CBDC accounts for corporations (the “intermediaries” the Fed refers to). The sponsors may want to close any loopholes there. That’s a quibble, however. This bill, sponsored by Rep. Tom Emmer (R-MO), Majority Whip of the House, with almost 80 co-sponsors, is a needed warning to the Fed and to surveillance hawks that a financial surveillance state is unacceptable. Man proposes, God disposes, but Congress often just kicks the can down the road.
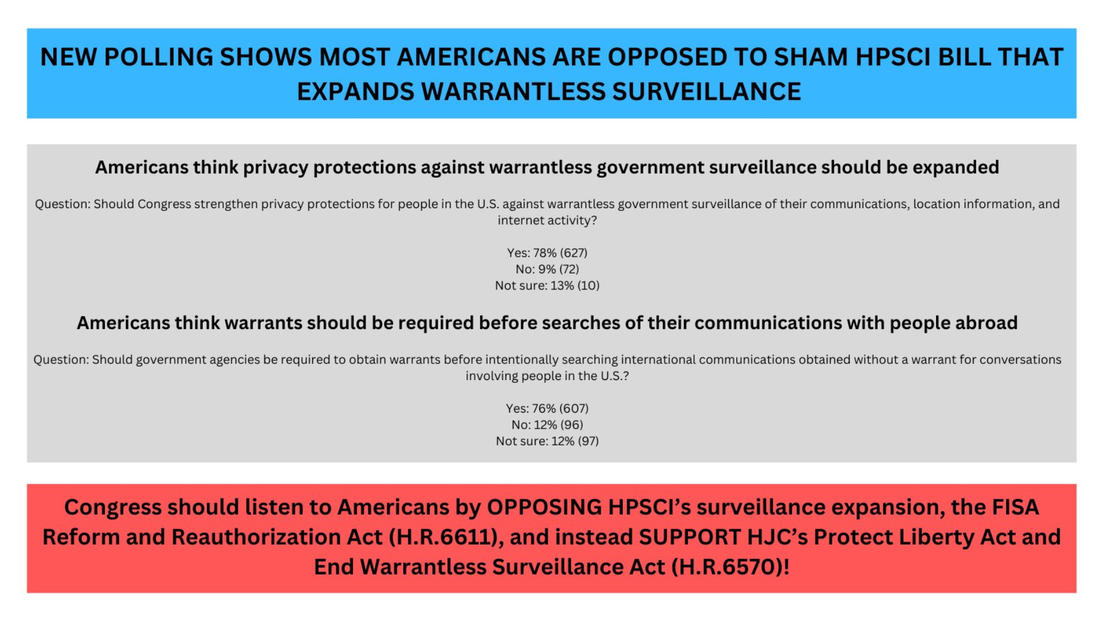
Throughout 2023, PPSA and our civil liberties allies made the case that Section 702 of the Foreign Intelligence Surveillance Act – enacted by Congress to give federal intelligence agencies the authority to surveil foreign threats abroad – has become a convenient excuse for warrantless domestic surveillance of millions of Americans in recent years. With Section 702 set to expire, the debate over reauthorizing this authority necessarily involves reforms and fixes to a law that functions in a radically different way than its Congressional authors imagined. In December, a strong bipartisan majority in the House Judiciary Committee passed a well-crafted bill to reauthorize FISA Section 702 – the Protect Liberty and End Warrantless Surveillance Act. This bill mandates a robust warrant requirement for U.S. person searches. It curtails the common government surveillance technique of “reverse targeting,” which uses Section 702 to work backwards to target Americans without a warrant. It also closes the loophole that allows government agencies to buy access to Americans’ most sensitive and personal information scraped from our apps and sold by data brokers. And the Protect Liberty Act requires the inclusion of lawyers with high-level clearances who are experts in civil liberties to ensure the secret FISA Court hears from them as well as from government attorneys. The FISA Reform and Reauthorization Act from the House Permanent Select Committee on Intelligence would not stop the widespread practice of backdoor searches of Americans’ information. And it does not address the outrageous practice of federal agencies buying up Americans’ most sensitive and private information from data brokers. In the crush of business, the deadline for reauthorizing Section 702 was delayed until early spring. Now the contest between the two approaches to Section 702 reauthorization begins in earnest. With a recent FreedomWorks/Demand Progress poll showing that 78 percent of Americans support strengthening privacy protections along the lines of those in the Protect Liberty Act, reformers go into the year with a strong tailwind. While we should never underestimate the guile of the intelligence community, reformers look to the debate ahead with hopefulness and eagerness to win this debate to protect the privacy of all Americans. In July, we wrote about revelations that the U.S. Department of Justice subpoenaed Google for the private data of House Intel staffers looking into the origins of the FBI’s Russiagate investigation. Then, in October, we wrote about a FOIA request from Empower Oversight seeking documents shedding light on the extent to which the executive branch is spying on Members of Congress. Now, following the launch of an official inquiry, Rep. Jim Jordan has issued a subpoena to Attorney General Merrick Garland for further information on the DOJ’s efforts to surveil Congress and congressional staff.
On Halloween, Jordan launched his inquiry into the DOJ’s apparent attempts to spy on Congress, sending letters to the CEOs of Alphabet, Apple, AT&T, T-Mobile, and Verizon requesting, for example, “[a]ll documents and communications between or among Apple employees and Justice Department employees referring or relating to subpoenas or requests issued by the Department of Justice to Apple for personal or official records or communications of Members of Congress or congressional staff….” Jordan also sent a letter to Garland, asserting that “[t]he Justice Department’s efforts to obtain the private communications of congressional staffers, including staffers conducting oversight of the Department, is wholly unacceptable and offends fundamental separation of powers principles as well as Congress’s constitutional authority to conduct oversight of the Justice Department.” Nearly two months later, according to Jordan, the DOJ’s response has been insufficient. In a letter to Garland dated December 19, 2023, Jordan says that the “Committee must resort to compulsory process” due to “the Department’s inadequate response to date.” That response, to be fair, did include a letter to Jordan dated December 4 conveying that the legal process used related to an investigation “into the unauthorized disclosure of classified information in a national media publication. Jordan, citing news reports, contends that the investigation actually “centered on FISA warrants obtained by the Justice Department on former Trump campaign associate Carter Page” (which the Justice Department Inspector General faulted for “significant inaccuracies and omissions”). Whatever the underlying motivation, Jordan is right to find DOJ’s explanation to date unsatisfying. Spying on Congress not only brings with it tremendous separation of powers concerns but raises a broader question about FISA and other processes that would reveal Americans’ personal information without sufficient predication. We need answers. Who authorized these DOJ subpoenas? And how can we make sure this kind of thing doesn’t happen again? PPSA looks forward to further developments in this story. Less consumer tracking leads to less fraud. That’s the key takeaway from a new study conducted by the National Bureau of Economic Research in its working paper, “Consumer Surveillance and Financial Fraud.”
Using data obtained from the Federal Trade Commission and the Consumer Financial Protection Bureau, as well as the geospatial data firm Safegraph, the authors looked at the correlation between Apple’s App Tracking Transparency framework and consumer fraud reports. Apple’s ATT policy requires user authorization before other apps can track and share customer data. In April 2021, Apple made this the default setting on all iPhones, ensuring that users would no longer be automatically tracked when they visit websites or use apps. This in turn dealt a hefty financial blow to companies like Snap, Facebook, Twitter, and YouTube, which collectively lost about $10 billion after implementation. The authors of the paper obtained fraud complaint figures from the FTC and the CFPB, then employed machine learning and targeted keyword searches to isolate complaints stemming from data privacy issues. They then cross-referenced those complaints with data acquired by Safegraph showing the number of iPhone users in a given ZIP code. According to the paper, a 10% increase in Apple users within a given ZIP code leads to a 3.21% reduction in financial fraud complaints. As the Electronic Frontier Foundation points out in a recent article about the study: “While the scope of the data is small, this is the first significant research we’ve seen that connects increased privacy with decreased fraud. This should matter to all of us. It reinforces that when companies take steps to protect our privacy, they also help protect us from financial fraud.” Obviously, more companies should follow Apple’s lead in implementing ATT-like policies. More than that, however, we need better and more robust laws on the books protecting consumer privacy. California has passed a number of related bills in recent years, most recently creating a one-stop opt-out mechanism for data collection. Colorado did the same. As other states and nations (and even CIA agents) wake up to the dangers of data tracking, this new study can serve as compelling, direct evidence showing why more restrictive settings – and consumer privacy – should always be the default. With Congress extending the reauthorization of FISA Section 702 until April, the debate over surveillance can be expected to fire up again when Members return in January. As Members relax and reorient over the holidays, we urge them to take a moment to listen to what the American people are saying.
The conservative FreedomWorks and the progressive Demand Progress, both highly respected advocacy organizations with deep grassroots, came together to conduct a national poll on the public’s approval of specific measures. Some of these measures are in the FISA Reform and Reauthorization Act passed by the House Intelligence Committee, and some in the Protect Liberty and End Warrantless Surveillance Act, passed 35-2 by the House Judiciary Committee. Across the board, Americans overwhelmingly support the provisions in the Protect Liberty Act.
House Judiciary Chairman Jim Jordan, writing in The Wall Street Journal, declared that, “in the wake of serious FISA abuses, our fidelity must be to the Constitution, not the surveillance state.” The FreedomWorks/Demand Progress poll shows that the American people agree. Just before Congress punted – delaying debate over reform proposals to Section 702 of the Foreign Intelligence Act – Sen. Mike Lee (R-UT) took to the Senate floor to describe how much is at stake for Americans.
Sen. Lee did not mince his words, saying Section 702 “is widely, infamously, severely abused” as “hundreds of thousands of American citizens have become victims of …warrantless backdoor searches.” The senator’s frustration boiled over when he spoke of questioning FBI directors in hearings, being told by them “don’t worry” because the FBI has strong procedures in place to prevent abuses. “We’re professionals,” they said. These promises from FBI directors, Sen. Lee said, are “like a curse,” an indication that the violation of Americans’ civil rights “gets worse every single time they say it.” The good news is that, although champions of reform fell short in Thursday’s vote, 35 senators in both parties were so bothered by the extension of Section 702 in its current form that they voted against its inclusion in the National Defense Authorization Act. What appears to be a temporary extension of Section 702 leaves the door open, we hope, for a fuller debate and vote on reform provisions early next year. When that happens, Sen. Lee will surely be in the lead. Here is the bipartisan honor roll of senators who voted in favor of surveillance reform. Tammy Baldwin (D-WI), Marsha Blackburn (R-TN), Cory Booker (D-NJ), Mike Braun (R-IN), Sherrod Brown (D-OH), Maria Cantwell (D-WA), Kevin Cramer (R-ND), Steve Daines (R-MT), Dick Durbin (D-IL), Chuck Grassley (R-IA), Bill Hagerty (R-TN), Josh Hawley (R-MO), Martin Heinrich (D-NM), Mazie Hirono (D-HI), John Hoeven (R-ND), Ron Johnson (R-WI), Mike Lee (R-UT), Ben Ray Lujan (D-NM), Cynthia Lummis (R-WY), Ed Markey (D-MA), Roger Marshall (R-KS), Robert Menendez (D-NJ), Jeff Merkley (D-OR), Rand Paul (R-KY), Bernie Sanders (I-VT), Eric Schmitt (R-MO), Rick Scott (R-FL), John Tester (D-MT),Tommy Tuberville (R-AL), Chris Van Hollen (D-MD), J.D. Vance (R-OH), Raphael Warnock (D-GA), Elizabeth Warren (D-MA), Peter Welch (D-VT), and Ron Wyden (D-OR). PPSA has often covered abuses of the geolocation tracking common to cellphones – from local governments in California spying on church-goers, to “warrant factories” in Virginia in which police obtain hundreds of warrants for thousands of surveillance days, often for minor infractions.
Geolocation tracking can be among the most pernicious compromises of personal privacy. In Carpenter v. United States (2018), the U.S. Supreme Court held that warrants are needed to inspect cellphone records extracted from cell-site towers, recognizing just how personal a target’s movements can be. Writing for the majority, Chief Justice John Roberts wrote: “Unlike the nosy neighbor who keeps an eye on comings and goings, they [new technologies] are ever alert, and memory is nearly infallible.” The narrowness of Carpenter has not, however, prevented the FBI and other federal agencies from tracking people’s movements without a warrant by merely buying their data from third-party data brokers. The FBI may soon, however, have much less to buy. Orin Kerr, writing in the Volokh Conspiracy in Reason, informs us that “Google will no longer keep location history even for the users who opted to have it turned on. Instead, the location history will only be kept on the user’s phones.” Kerr adds: “If Google doesn’t keep the records, Google will have no records to turn over.” A corporate decision in Silicon Valley has thus removed a major pillar of government surveillance. It says something about the current state of this country when a Big Tech giant is more responsive to consumers than government is to its citizens. But don’t be surprised if the feds start to pressure Google to reverse its decision. WSJ Graphical Roadmap: How Your Personal Information Migrates from App, to Broker, to the Government12/5/2023
A report in The Wall Street Journal does a masterful job of combining graphics and text to illustrate how technology embedded in our phones and computers to serve up ads also enables government surveillance of the American citizenry.
The WSJ has identified and mapped out a network of brokers and advertising exchanges whose data flows from apps to Defense Department, intelligence agencies, and the FBI. The WSJ has compiled this information into several illustrative animated graphs that bring the whole scheme to life. Here’s how it works: As soon as you open an ad-supported app on your phone, data from your device is recorded and transmitted to buyers. The moment before an app serves you an ad, all advertisers in the bidding process are given access to information about your device. The first information up for bids is your location, IP address, device, and browser type. Ad services also record information about your interests and develop intricate assumptions about you. Many data brokers regularly sell Americans’ information to the government, where it may be used for cybersecurity, counterterrorism, counterintelligence, and public safety – or whatever a federal agency deems as such. Polls show that Americans are increasingly concerned about their digital privacy but are also fatalistic and unaware about their privacy options as consumers. According to a recent poll by Pew published last month, 81 percent of U.S. adults are concerned about how companies use the data they collect. Seventy-one percent are concerned about how the government uses their data, up from 64 percent in 2019. There is also an increasing feeling of helplessness: 73 percent of adults say they have little to no control over what companies do with their data, while 79 percent feel the same towards the government. The number of concerned Americans rises to 89 percent when the issue of children’s online privacy is polled. Crucially, 72 percent of Americans believe there should be more regulation governing the use of digital data. Despite high levels of concern, nearly 60 percent of Americans do not read the privacy policies of apps and social media services they use. Most Americans do not have the time or legal expertise to carefully study every privacy policy they encounter. Given that one must accept these terms or not be online, it is simply impractical to expect Americans do so. Yet government agencies assert that it is acceptable to collect and review Americans’ most personal data without a warrant because we have knowingly signed away our rights. There is good news. In the struggle for government surveillance reform currently taking place on Capitol Hill – and the introduction of the Protect Liberty and End Warrantless Surveillance Act – Americans are getting a better understanding of the costs of being treated as digital chattel by data brokers and government. |
Categories
All
|



















 RSS Feed
RSS Feed