Today, Laredo – Tomorrow, Los Angeles and Little Rock? When the U.S. military dispatches a drone to strike a target, it often uses a wireless device detection system that can correlate signals from terrorists’ cellphones and other devices emanating from within a target vehicle. Under such circumstances, calls and other signals from terrorists’ devices lead missiles straight into a target’s car.
As law and order along the U.S. border breaks down, it is not surprising that two Texas jurisdictions – Webb and Val Verde counties – purchased such military-grade wireless detection systems. NOTUS.org reports that law enforcement along the border can detect in-vehicle wireless signals and merge them with systems that track vehicles’ license plates to isolate a given car. This is yet another sign that the U.S. Supreme Court urgently needs to revisit the limits that federal and local law enforcement agencies are placing on the Court’s 2018 Carpenter opinion, which requires a probable cause warrant before officers can use cell tower GPS data to access a suspect’s location history. Agencies have not internalized the basic principles of that ruling. Instead, they’ve rationalized that if they are not specifically accessing historical cell tower data, they are complying with the law. To be fair, parts of the border are beginning to resemble a war zone, with out-of-control illegal immigration organized by criminal cartels. Given the current lawless state of the U.S.-Mexican border, local governments are using Department of Justice grants to purchase systems similar to those used by the U.S. military and CIA. Captain Federico Calderon of the Sheriff’s office of Webb County, which includes the large border city of Laredo, told NOTUS that the county purchased a “very restricted” version. Capt. Calderon said that Webb County is using this technology as a pilot program to scan for signals coming from the empty quarters of ranches where no one should be. Val Verde County did not respond to NOTUS’s questions. The potential for widespread abuse of this technology rivals that of cell-site simulators and data purchases. NOTUS reports “as people walk around with headphones, fitness wearables and other devices, emitting a cloud of radio frequency signals unique to them, their data can be linked to a car, even after they have ditched the car.” Local law enforcement officials want such technology to identify human traffickers and cartel smugglers. It is doubtful, however, that this technology will remain restricted to such narrow purposes. And as with purchased data and cellsite simulators, the introduction of this new militarized technology compromises the privacy of many more people – friends, family, and bystanders. “We are well beyond the idea that people have no privacy in public,” Jennifer Grannick of the American Civil Liberties Union told NOTUS. “Here, they’re installing this mass surveillance system.” With the spread of often violent political protests across the nation, a high level of terror alert from the FBI, and college campuses convulsed by tent cities, there will be no lack of reasons for law enforcement to add one more capability to what is evolving into a national surveillance state. It is reasonable to use technology to control the border. But it is up to Congress and the courts to keep a close eye on the widespread introduction of military wireless device detection systems to track Americans. Why did the “unmasking” of Americans’ identities in the global data trawl of U.S. intelligence agencies increase by 172 percent, from 11,511 times in 2022 to 31,330 times in 2023?
Government officials briefing the media say that most of this increase was a defensive response to a hostile intelligence agency launching a massive cyberattack on U.S. infrastructure, possibly infiltrating the digital systems of dams, power plants, or the like. What we do know for sure is that this authority has been abused before. Unmasking occurs when American citizens or “U.S. persons” are caught up, incidentally, in warrantless foreign surveillance. When this happens, the identities of these Americans are routinely hidden from government agents, or “masked.” But senior officials can request that the NSA “unmask” those individuals. This should be a relatively rare occurrence. Yet for some reason, over a 12-month period between 2015 and 2016, the Obama Administration unmasked 9,217 persons. Former UN Ambassador Samantha Power, or someone acting in her name, was a prolific unmasker. Power’s name was used to request unmasking of Americans more than 260 times. Large-scale unmasking continued under the Trump administration, with 2018 seeing 16,721 unmaskings, an increase of 7,000 from the year before. In recent years, the number hovered around 10,000. Now it is three times that many. This is a concern if some subset of these unmaskings (which mostly involve an email account or IP address, not a name) were for named individuals for political purposes. Consider that in 2016, at least 16 Obama administration officials, including then-Vice President Joe Biden, requested unmaskings of Donald Trump’s advisors. Outgoing National Security Advisor Susan Rice took a particular interest in unmasking members of President-elect Trump’s transition team. We are left to wonder if all of this rise in unmasking numbers can be explained away by Chinese or Russian hackers, or if some portion of them reflect the use of this authority for political purposes. Were prominent politicians, officeholders, or candidates unmasked? These raw numbers come from the government’s Annual Statistical Transparency report. This report on intelligence community activities from the Office of the Director of National Intelligence offers revealing numbers, but often without detail or explanation that would explain such jumps. All we have to rely on are media briefs that at times seem more forthcoming than the briefings available to Members of Congress, even those tasked with oversight of intelligence agencies in the House and Senate Judiciary Committees. As these numbers rise, the American people deserve more information and a solid assurance that these authorities will never again be used for political purposes by either party. Five Maine lobstermen are suing Maine’s Department of Marine Resources after the agency issued regulations requiring electronic tracking of vessels fishing in federal waters. The plaintiffs allege such tracking violates privacy rights, due process, and equal protection under the Constitution. It’s a red-hot, lobster pot controversy with significant implications on the ever-evolving body of law surrounding geolocation tracking and surveillance.
Maine adopted the tracking regulation in December to comply with a requirement issued by the Atlantic States Marine Fisheries Commission, whose overarching policy objective here is to help protect the North Atlantic right whale. This is certainly a noble objective, but it brings with it troubling implications. Maine Department of Marine Resources Commissioner Patrick Keliher makes the argument that because lobstermen work in a “closely regulated industry,” they have “a greatly reduced expectation of privacy.” It’s a common refrain for those seeking to impose new surveillance measures. But as attorney John Vecchione of the New Civil Liberties Alliance once said, “the expansion of closely regulated-industry theory is a huge, huge danger to liberties for everybody.” Indeed, as society, the economy, and ensuing regulations grow, simply having to get a license could subject any business to warrantless inspections. Such an argument could be used to attach trackers to realtors as they move around from house to house, salespersons, contractors, or any other group of mobile professionals. The U.S. District Court for the District of Maine, where the case was filed, might take a page from the Fifth Circuit, which in 2023 struck down a U.S. Department of Commerce requirement that would have forced charter boat owners to install, at their own expense, a “vessel monitoring system” that would continuously transmit their boats’ location, regardless of whether it was being used for commercial or personal purposes. In that case, the court found that it “borders on incredible” that the government claimed it failed to notice personal privacy concerns in public comments to its rule. The court, further, found that discovery of prime fishing spots in the Gulf would constitute a hardship for many charter operators. Similarly, attorneys for the suing lobstermen argue that they “jealously guard the whereabouts and the techniques they use to place their traps. This is directly correlated to their ability to make a living.” It’s not just fishing locations that are at risk, however. The U.S. Supreme Court has repeatedly held that warrantless GPS tracking constitutes an unlawful search. Tracking someone’s movements, it needn’t be emphasized, can reveal quite a lot about their personal and private lives. As the Maine federal court considers these issues, we side unequivocally with the lobstermen. Simply put, there must be a way to balance the privacy interests of fishermen and the policy objective of protecting marine life. Top-down surveillance mandates seem a poor fit. Surveillance is key to fighting crime and catching criminals, but the same system that protects us also endangers the privacy and security of ordinary citizens. It would be naïve to imagine that mass and indiscriminate surveillance will only be used against the “bad guys” – or that we can even all agree on who the “bad guys” are over time.
Such concerns come to top of mind with stories, like that of California Gov. Gavin Newsom, who recently announced a plan to combat crime in Oakland by installing 480 high-tech cameras on the city’s busiest roads and freeways to catch criminals. As commendable as that sounds, we have to ask what else it will catch – and what will local and state law enforcement do with all that information? These cameras will capture the make and model of vehicles, as well as read license plates, alerting police if a suspect’s vehicle is spotted. Installed with support from four large corporations with a presence in the Bay Area, it’s a fair bet that these cameras are likely very popular with residents. Oakland has seen skyrocketing rates of crime, with car jackings, thefts, and armed robberies becoming commonplace. The city recently made national news when the iconic In-N-Out burger chain shuttered its first restaurant in Oakland out of concern for its employees. The planned installation of mass surveillance on Oakland’s streets is just the latest story in a national trend. The left-leaning Atlanta Community Press Collective reports that local law enforcement in Atlanta is promoting an electronic surveillance system of people who wear court-ordered electronic monitoring while on parole or awaiting trial. Talitrix, a surveillance company, “uses geofencing and proprietary algorithms to produce a ‘Talitrix score’ that agencies can use to determine whether someone’s behavior on pretrial release or probation should subject them to re-arrest and incarceration.” Talitrix proposes to integrate its technology with that of another surveillance firm, Fusus, which supports Atlanta’s expansive camera network. That network links public video feeds with those from stores, shopping malls, apartment buildings, and homes to combine public and private cameras to give the police constant citywide surveillance. The Atlanta Community Press Collective reports that integration “would combine GPS-enabled digital shackles featuring biometric monitoring capabilities with the growing canopy of Fusus-linked video cameras” across Atlanta. This system would put up to 900 people under constant video, audio, biometric, and GPS surveillance during their pre-trial release, placing them in what Cooper Quinton of the Electronic Frontier Foundation calls “an open-air prison.” Quinton added, “Even if you have not yet been convicted of a crime under this system, you and your family could be subject to constant, targeted video surveillance.” Video surveillance and automated license plate readers combine with local use of cell-site simulators (which follow a cellphone user’s location), facial recognition, aerial video surveillance, “predictive policing,” location tracking, and social media monitoring to create a system of continuous surveillance. Add AI into the mix, and you have all the elements to create a Chinese-style surveillance state. The expansion of surveillance is being done, as we have seen in Oakland, with the admirable intention of curbing runaway crime. Without proper safeguards and limits on how collected data can be used, however, the knitting together of all these data streams makes the potential for Orwellian surveillance all but certain. Our choices come down to tradeoffs between security and freedom. We can limit access to surveillance without a warrant and apply limits on data collection. Otherwise, China shows us the consequences of a complete sacrifice of liberty for security – you get neither as the government becomes the greatest threat to both. To learn what your local government can do with technology check out the Electronic Frontier Foundation’s updated Street Level Surveillance hub. In the meanwhile, we all need to understand that there are tradeoffs between increased safety and reduced privacy. There is a tipping point, which we are approaching, in which the networks that protect us can become the new threat. Byron Tau – journalist and author of Means of Control, How the Hidden Alliance of Tech and Government Is Creating a New American Surveillance State – discusses the details of his investigative reporting with Liza Goitein, senior director of the Brennan Center for Justice's Liberty & National Security Program, and Gene Schaerr, general counsel of the Project for Privacy and Surveillance Accountability.
Byron explains what he has learned about the shadowy world of government surveillance, including how federal agencies purchase Americans’ most personal and sensitive information from shadowy data brokers. He then asks Liza and Gene about reform proposals now before Congress in the FISA Section 702 debate, and how they would rein in these practices. A federal court has given the go-ahead for a lawsuit filed by Just Futures Law and Edelson PC against Western Union for its involvement in a dragnet surveillance program called the Transaction Record Analysis Center (TRAC).
Since 2022, PPSA has followed revelations on a unit of the Department of Homeland Security that accesses bulk data on Americans’ money wire transfers above $500. TRAC is the central clearinghouse for this warrantless information, recording wire transfers sent or received in Arizona, California, New Mexico, Texas, and Mexico. These personal, financial transactions are then made available to more than 600 law enforcement agencies – almost 150 million records – all without a warrant. Much of what we know about TRAC was unearthed by a joint investigation between ACLU and Sen. Ron Wyden (D-OR). In 2023, Gene Schaerr, PPSA general counsel, said: “This purely illegal program treats the Fourth Amendment as a dish rag.” Now a federal judge in Northern California determined that the plaintiffs in Just Future’s case allege plausible violations of California laws protecting the privacy of sensitive financial records. This is the first time a court has weighed in on the lawfulness of the TRAC program. We eagerly await revelations and a spirited challenge to this secretive program. The TRAC intrusion into Americans’ personal finances is by no means the only way the government spies on the financial activities of millions of innocent Americans. In February, a House investigation revealed that the U.S. Treasury’s Financial Crimes Enforcement Network (FinCEN) has worked with some of the largest banks and private financial institutions to spy on citizens’ personal transactions. Law enforcement and private financial institutions shared customers’ confidential information through a web portal that connects the federal government to 650 companies that comprise two-thirds of the U.S. domestic product and 35 million employees. TRAC is justified by being ostensibly about the border and the activities of cartels, but it sweeps in the transactions of millions of Americans sending payments from one U.S. state to another. FinCEN set out to track the financial activities of political extremists, but it pulls in the personal information of millions of Americans who have done nothing remotely suspicious. Groups on the left tend to be more concerned about TRAC and groups on the right, led by House Judiciary Chairman Jim Jordan, are concerned about the mass extraction of personal bank account information. The great thing about civil liberties groups today is their ability to look beyond ideological silos and work together as a coalition to protect the rights of all. For that reason, PPSA looks forward to reporting and blasting out what is revealed about TRAC in this case in open court. Any revelations from this case should sink in across both sides of the aisle in Congress, informing the debate over America’s growing surveillance state. The best intentions of Amazon to reduce easy, warrantless surveillance of the American people are being undermined by cheap, Chinese cameras.
PPSA has long tracked the privacy threat of Amazon’s cooperative agreements with more than 2,000 police and fire departments to solicit Ring videos for neighborhood surveillance from customers. In January, we celebrated Amazon’s disabling of its Request for Access tool, a feature that facilitated requests from law enforcement to ask Ring camera owners to volunteer video of their neighbors and neighborhood. The Electronic Frontier Foundation was so impressed by Amazon’s move that they removed Ring from its Atlas of Surveillance, a comprehensive, national map of points of police surveillance. In March, EFF removed 2,530 data points from its Atlas because Amazon will no longer facilitate warrantless requests for consumer video footage. As EFF notes, this does not mean that the police won’t still be able to access Ring footage. PPSA reported in February that law enforcement in central Texas are ho-hum about Amazon’s policy change, telling reporters they will simply appeal to individual households to ask for videos. But at least this means police requests will be tied to actual events, requiring an expenditure of shoe leather after a burglary, car accident, or fire, instead of a broad array of surveillance footage available for police to examine. Around the same time, journalists Stacey Higginbotham and Daniel Wroclawski of Consumer Reports (CR) demonstrated the alarming vulnerability of cheap, Chinese doorbell cameras sold by Amazon, as well as by Walmart, Sears, and Chinese online retailers Shein and Temu. These cameras are sold by the thousands under an ever-shifting array of brand names, but all are connected to the same app called Awit, owned by Shenzen-based Eken Group Ltd., and apparently managed in North America out of an apartment in east Los Angeles County. Higginbotham and Wroclawski reported that with the use of the Awit app, these cameras were easily compromised and used for remote surveillance of their owners – the exact opposite of the purpose of a security camera. They wrote: “People who face threats from a stalker or estranged abusive partner are sometimes spied on through their phones, online platforms, and connected smartphone devices. The vulnerabilities CR found could allow a dangerous person to take control of the video doorbell on their target’s home, watching when they and their family members come and go.” Worse, these doorbells expose their owners’ home IP address and Wi-Fi network name to the internet without encryption. They also lack a visible ID issued by the Federal Communications Commission, making them illegal to sell in the United States. Weeding out junk products is probably a difficult task for Amazon, given the shape-shifting, brand-changing nature of some providers. Like many Chinese-made products, these doorbell cameras are booby-trapped, either through sloppiness or by intention, or perhaps both. It doesn’t take a lot of imagination to envision them being used against U.S. officials, civilian or military, by Chinese intelligence during a crisis. Imagine the intelligence value of seeing National Security Council personnel leaving their homes at the same time around 2 a.m. Amazon’s top search results showed few of these Chinese cameras available now, though it is hard to tell given the plethora of ever-changing brand names. Perhaps Amazon products should come with a cautionary “China” sticker for consumers. U.S. Treasury and FBI Targeted Americans for Political BeliefsThe House Judiciary Committee and its Select Subcommittee on the Weaponization of the Federal Government issued a report on Wednesday revealing secretive efforts between federal agencies and U.S. private financial institutions that “show a pattern of financial surveillance aimed at millions of Americans who hold conservative viewpoints or simply express their Second Amendment rights.”
At the heart of this conspiracy is the U.S. Treasury Department’s Financial Crimes Enforcement Network (FinCEN) and the FBI, which oversaw secret investigations with the help of the largest U.S. banks and financial institutions. They did not lack for resources. Law enforcement and private financial institutions shared customers’ confidential information through a web portal that connects the federal government to 650 companies that comprise two-thirds of the U.S. domestic product and 35 million employees. This dragnet investigation grew out of the aftermath of the Jan. 6 riot in the U.S. Capitol, but it quickly widened to target the financial transactions of anyone suspiciously MAGA or conservative. Last year we reported on how the Bank of America volunteered the personal information of any customer who used an ATM card in the Washington, D.C., area around the time of the riot. In this newly revealed effort, the FBI asked financial services companies to sweep their database to look for digital transactions with keywords like “MAGA” and “Trump.” FinCEN also advised companies how to use Merchant Category Codes (MCC) to search through transactions to detect potential “extremists.” Keywords attached to suspicious transactions included recreational stores Cabela’s, Bass Pro Shop, and Dick’s Sporting Goods. The committee observed: “Americans doing nothing other than shopping or exercising their Second Amendment rights were being tracked by financial institutions and federal law enforcement.” FinCEN also targeted conservative organizations like the Alliance Defending Freedom or the Eagle Forum for being demonized by a left-leaning organization, the Institute for Strategic Dialogue in London, as “hate groups.” The committee report added: “FinCEN’s incursion into the crowdfunding space represents a trend in the wrong direction and a threat to American civil liberties.” One doesn’t have to condone the breaching of the Capitol and attacks on Capitol police to see the threat of a dragnet approach that lacked even a nod to the concept of individualized probable cause. What was done by the federal government to millions of ordinary American conservatives could also be done to millions of liberals for using terms like “racial justice” in the aftermath of the riots that occurred after the murder of George Floyd. These dragnets are general warrants, exactly the kind of sweeping, indiscriminate violations of privacy that prompted this nation’s founders to enact the Fourth Amendment. If government agencies cannot satisfy the low hurdle of probable cause in an application for a warrant, they are apt to be making things up or employing scare tactics. If left uncorrected, financial dragnets like these will support a default rule in which every citizen is automatically a suspect, especially if the government doesn’t like your politics. China is planning to build a large base on the moon in the 2030s, with science labs, housing for astronauts, and a fleet of robots. It is also planning to bring up the advanced technologies that enable its 600-million camera Skynet system to surveil the Chinese people.
“Skynet” is, of course, familiar to American ears as the AI villain in the Terminator movies. It is also the actual term China uses in English for its surveillance network, a term deriving from an ancient Chinese proverb that includes the line, “There is forever a net in the sky.” Stephen Chen of the South China Morning Post informs us that the meaning here is that those who do wrong or resist the regime will not escape the celestial net. China’s experience with the Skynet system, which fields two cameras for every Chinese adult, has taught the regime how to manage such amounts of surveillance data. This knowledge will be useful in building out a Skynet for the moon. The purpose, say Chinese aerospace agencies, is to create a massive video surveillance system that is “capable of identifying, locating, tracking and aiming at suspicious targets independently.” If so, perhaps the moon really will be looking down on us. When we covered a Michigan couple suing their local government for sending a drone over their property to prove a zoning violation, we asked if there are any legal limits to aerial surveillance of your backyard.
In this case before the Michigan Supreme Court, Maxon v. Long Lake Township, counsel for the local government said that the right to inspect our homes goes all the way to space. He described the imaging capability of Google Earth satellites, asking: “If you want to know whether it’s 50 feet from this house to this barn, or 100 feet from this house to this barn, you do that right on the Google satellite imagery. And so given the reality of the world we live in, how can there be a reasonable expectation of privacy in aerial observations of property?” One justice reacted to the assertion that if Google Earth could map a backyard as closely and intimately as a drone, that would be a search. “Technology is rapidly changing,” the justice responded. “I don’t think it is hard to predict that eventually Google Earth will have that capacity.” Now William J. Broad of The New York Times reports that we’re well beyond Google Earth’s imaging of barns and houses. Try dinner plates and forks. Albedo Space of Denver is making a fleet of 24 small, low orbit satellites that will use imagery to guide responders in disasters, such as wildfires and other public emergencies. It will improve the current commercial standard of satellite imaging from a focal length of about a foot to about four inches. A former CIA official with decades of satellite experience told Broad that it will be a “big deal” when people realize that anything they are trying to hide in their backyards will be visible. Skinny-dipping in the pool will only be for the supremely confident. To his credit, Albedo chief Topher Haddad said, “we’re acutely aware of the privacy implications,” promising that management will be selective in their choice of clients on a case-by-case basis. It is good to know that Albedo likely won’t be using its technology to catch zone violators or backyard sunbathers. We’ve seen, however, that what is cutting-edge technology today will be standard tomorrow. This is just one more way in which the velocity of technology is outpacing our ability to adjust. There is, of course, one effective response. We can reject the Michigan town’s counsel argument who said, essentially, that privacy’s dead and we should just get over it. Courts and Congress should define orbital and aerial surveillance as searches requiring a probable cause warrant, as defined by the Fourth Amendment of the U.S. Constitution, before our homes and backyards can be invaded by eyes from above. The greatest danger to privacy is not that Albedo will allow government snoops to watch us in real time. The real threat is a satellite company’s ability to collect private images by the tens of millions. Such a database could then be sold to the government just as so much commercial digital information is now being sold to the government by data brokers. This is all the more reason for Congress to import the privacy-protecting warrant provisions of the Fourth Amendment Is Not For Sale Act into the reauthorization of FISA Section 702. In the last century, the surveillance state was held back by the fact that there could never be enough people to watch everybody. Whether Orwell’s fictional telescreens or the East German Stasi’s apparatus of civilian informants, there could simply never be enough watchers to follow every dissident, while having even more people to put all the watcher’s information together (although the Stasi’s elaborate filing system came as close as humanly possible to omniscience).
Now, of course, AI can do the donkey work. It can decide when a face, or a voice, a word, or a movement, is significant and flag it for a human intelligence officer. AI can weave data from a thousand sources – cell-site simulators, drones, CCTV, purchased digital data, and more – and thereby transform data into information, and information into actionable intelligence. The human and institutional groundwork is already in place to feed AI with intelligence from local, national, and global sources in more than 80 “fusion centers” around the country. These are sites where the National Counterterrorism Center coordinate intelligence from the 17 federal intelligence agencies with local and state law enforcement. FBI, NSA, and Department of Homeland Security intelligence networks get mixed in with intelligence from the locals. If you’ve ever reported something suspicious to the “if you see something, say something” ads, a fusion center is where your report goes. With terrorists and foreign threats ever present, it makes sense to share intelligence between agencies, both national and local. But absent clear laws and constitutional limits, we are also building the basics of a full-fledged surveillance state. With no warrant requirements currently in place for federal agencies to inspect Americans’ purchased digital data, there is nothing to stop the fusion of global, national, and local intelligence from a thousand sources into one ever-watchful eye. Step by step, day by day, new technologies, commercial entities and government agencies add new sources and capabilities to this ever-present surveillance. The latest thread in this weave comes from Axon, the maker of Tasers and body cameras for police. Axon has just acquired Fusus, which grants access to the camera networks of shopping centers, hospitals, residential communities, houses of worship, schools, and urban environments for more than 250 police “real-time crime centers.” Weave that data with fusion centers, and voilà, you are living in a Panopticon – a realm where you are always seen and always heard. To make surveillance even more thorough, Axon’s body cameras are being sold to healthcare and retail facilities to be worn by employees. Be nice to your nurse. Such daily progress in the surveillance state provides all the more reason for the U.S. House in its debate over the reauthorization of FISA Section 702 to include a warrant requirement before the government can freely swim in this ocean of data – our personal information – without restraint. The word from Capitol Hill is that Speaker Mike Johnson is scheduling a likely House vote on the reauthorization of FISA’s Section 702 this week. We are told that proponents and opponents of surveillance reform will each have an opportunity to vote on amendments to this statute.
It is hard to overstate how important this upcoming vote is for our privacy and the protection of a free society under the law. The outcome may embed warrant requirements in this authority, or it may greatly expand the surveillance powers of the government over the American people. Section 702 enables the U.S. intelligence community to continue to keep a watchful eye on spies, terrorists, and other foreign threats to the American homeland. Every reasonable person wants that, which is why Congress enacted this authority to allow the government to surveil foreign threats in foreign lands. Section 702 authority was never intended to become what it has become: a way to conduct massive domestic surveillance of the American people. Government agencies – with the FBI in the lead – have used this powerful, invasive authority to exploit a backdoor search loophole for millions of warrantless searches of Americans’ data in recent years. In 2021, the secret Foreign Intelligence Surveillance Court revealed that such backdoor searches are used by the FBI to pursue purely domestic crimes. Since then, declassified court opinions and compliance reports reveal that the FBI used Section 702 to examine the data of a House Member, a U.S. Senator, a state judge, journalists, political commentators, 19,000 donors to a political campaign, and to conduct baseless searches of protesters on both the left and the right. NSA agents have used it to investigate prospective and possible romantic partners on dating apps. Any reauthorization of Section 702 must include warrants – with reasonable exceptions for emergency circumstances – before the data of Americans collected under Section 702 or any other search can be queried, as required by the U.S. Constitution. This warrant requirement must include the searching of commercially acquired information, as well as data from Americans’ communications incidentally caught up in the global communications net of Section 702. The FBI, IRS, Department of Homeland Security, the Pentagon, and other agencies routinely buy Americans’ most personal, sensitive information, scraped from our apps and sold to the government by data brokers. This practice is not authorized by any statute, or subject to any judicial review. Including a warrant requirement for commercially acquired information as well as Section 702 data is critical, otherwise the closing of the backdoor search loophole will merely be replaced by the data broker loophole. If the House declines to impose warrants for domestic surveillance, expect many politically targeted groups to have their privacy and constitutional rights compromised. We cannot miss the best chance we’ll have in a generation to protect the Constitution and what remains of Americans’ privacy. Copy and paste the message below and click here to find your U.S. Representative and deliver it: “Please stand up for my privacy and the Fourth Amendment to the U.S. Constitution: Vote to reform FISA’s Section 702 with warrant requirements, both for Section 702 data and for our sensitive, personal information sold to government agencies by data brokers.” We recently celebrated the decision by Amazon to require police to present a warrant before going through the “Request for Assistance” tool to seek video footage from the neighborhood networks of Ring cameras owners. We touted this is as a significant victory for privacy.
And it is – it effectively neutralized more than 2,300 agreements Amazon had with local police and fire departments to help them obtain private security footage – but it wasn’t quite as big a deal as we first thought. Thanks to reporting from Baylee Bates of KCEN News in Temple, Texas, Amazon’s change is prompting a big yawn from police. Why? A spokeswoman for the Temple Police Department told Bates that officers had found greater success in requests for video footage by making door-to-door contacts. “We have found throughout the years of gathering the security footage that going to residents, business owners, that face-to-face interaction with people has been way more successful for us,” said Megan Price of the Temple PD. A spokesman for the Bell County Sheriff’s Department told Bates that Amazon’s policy change “doesn’t stop us from going individual-to-individual and talking, the way we prefer to do it anyway.” Since the introduction of Ring, customers have for the most part complied with police requests for videos. If someone set fire to a car in our neighborhood, or burgled a house across the street, we would do the same. But the eagerness of most people to grant police access to surveillance video is concerning, as more neighborhoods become “ringed” with surveillance. Three years ago, a Washington Post story quoted a mother in California telling her seven-year-old son, “Every time you ride your bike down this block, there are probably 50 cameras that watch you going past. If you make a bad choice, those cameras will catch you.” We wrote at the time that George Orwell never imagined millions of Ring cameras – and millions of users willing to hand over video when asked. The threat to privacy from neighborhood surveillance is as much about audio recordings as it is video. Sen. Edward Markey (D-MA) assessed the risk of a surveillance network in every neighborhood in a letter to Amazon in 2022: “This surveillance system threatens the public in ways that go far beyond abstract privacy invasion: individuals may use Ring devices’ audio recordings to facilitate blackmail, stalking, and other damaging practices. As Ring products capture significant amounts of audio on private and public property adjacent to dwellings with Ring doorbells – including recordings of conversations that people reasonably expect to be private – the public’s right to assemble, move, and converse without being tracked is at risk.” At least you can always step inside, away from the microphones and the cameras, settle into your chair, and let Alexa take over your surveillance. Cato Institute Senior Fellow Patrick Eddington filed a Freedom of Information Act request against the Department of Defense this week asking two questions.
First, what was the scope and duration of Pentagon aerial surveillance deployed over domestic protesters in the last year of the Trump Administration? Second, why is the Biden Administration shielding those records from the public? In the world of civil liberties critics of the American surveillance state, Patrick Eddington has the pedigree of highly credentialed practitioner. From 1988 to 1996, Eddington was a military imagery analyst at the CIA’s National Photographic Interpretation Center, where he was officially recognized many times for his work. He’s the real deal. So is former Rep. Adam Kinzinger (R-IL), who knows what he’s talking about when it comes to surveillance aircraft. Kinzinger flew the RC-26 surveillance aircraft in Iraq, which had a complement of sensors that records people and objects with video, in both visible and infrared frequencies. Eddington reports that from 2020 to 2021, the Pentagon used RC-26B turboprop planes to surveil American protesters. Many of these aircraft have been deployed widely across the country, from Alabama to Washington State. Kinzinger has written that the RC-26 “could fly fast and low, capturing the signals from thousands of cellphones … With the right coordination, the target could be reached in minutes, not hours.” The Air Force Inspector General reports that the digital data packages Kinzinger referred to were removed for the RC-26s deployed for domestic use. Even so, the sensor package of this fleet still represents an astonishing surveillance capability of Americans on the ground. Writing in The Orange County Register, Eddington asks if the Biden Administration’s stonewalling means it reserves the right to use the fleet against pro-Trump protesters? Or for a new Trump Administration in tracking anti-Trump protesters? Or for some future president against any political enemy? Behind the intense rancor in American partisan politics, at least one aspiration unites administrations of both parties – an intent to surveil. PPSA will report on further developments. We reported last week that the Biden Administration leaked the news that it is drafting an executive order to restrict “countries of concern” from acquiring Americans’ most sensitive and personal digital and DNA information.
At the top of the Administration’s concern is the likely acquisition by the People’s Republic of China of a vast databank of Americans’ DNA from Chinese-owned companies that perform genetic testing for U.S. healthcare. Should we care? A glimpse of the dangers of such tracking can be seen in how China uses mass DNA mapping of whole populations to track and persecute religious minorities. At a recent conference in Washington, D.C., on surveillance of religious minorities in China, we heard evidence – well documented by many journalists – that China is using facial recognition (with racial filters), car sensors, cell-site simulators, and location tracking to systematically surveil that country’s Uighur Muslim and Tibetan Buddhist minorities. A recent Human Rights Watch whitepaper details how China’s authorities are systematically collecting DNA in Tibet. The cover story for one such program for people aged 12 to 65 is that the government is performing a health-check program called Physicals For All – though patients are not allowed to learn the results of any of their tests. DNA testing in Tibet is, to paraphrase the Godfather, an offer that cannot be refused. With this data, the government can track people by ethnicity, and map their families by their genes and presumed beliefs. The most pernicious aspect of this program is the collection of children’s DNA, a unique identifier that will never change. Such genetic surveillance also necessarily connects a whole bloodline to one person suspected of religious dissidence – what Chinese police call “one household, one file.” Such files can be used to track people who lead worship services or advocate religious or secular views not approved by the government. This program of police-community relations is called “spreading information tentacles.” DNA is also used to identify (and presumably, from samples located at a given site or shrine) to track clerics and lamas, village elders, and others who might be engaged in meetings or conducting unofficial mediation of local disputes. Combined with electronic surveillance, authorities can detect forbidden material accessed by phones and other devices, and then turn to DNA mapping to break up social and religious organizations, keeping civil society atomized before the state. Thus, China’s DNA database is amplified by many forms of electronic surveillance, with artificial intelligence putting together patterns of association and blood relations for police. Researcher Adrian Zenz told The Bulletin of Atomic Scientists that in 2017 alone, China spent almost $350 billion on internal security outlays. According to the Biden Administration, China is also spending money to purchase Americans’ data. This could include medical, financial, occupational, familial, and romantic profiles: genetic surveillance provides another tile that forms a mosaic of the American population for China. Thus, an American child sequenced for a medical test today could have his or her genetic health profile and identity known to the Chinese state for life. As the Office of the Director of National Intelligence warns: “The loss of your DNA not only affects you, but your relatives and, potentially, generations to come.” Wired reports that police in northern California asked Parabon NanoLabs to run a DNA sample from a cold case murder scene to identify the culprit. Police have often run DNA against the vast database of genealogical tests, cracking cold cases like the Golden State Killer, who murdered at least 13 people.
But what Parabon NanoLabs did for the police in this case was something entirely different. The company produced a 3D rendering of a “predicted face” based on the genetic instructions encoded in the sample’s DNA. The police then ran it against facial recognition software to look for a match. Scientists are skeptical that this is an effective tool given that Parabon’s methods have not been peer-reviewed. Even the company’s director of bioinformatics, Ellen Greytak, told Wired that such face predictions are closer in accuracy to a witness description rather than the exact replica of a face. With the DNA being merely suggestive – Greytak jokes that “my phenotyping can tell you if your suspect has blue eyes, but my genealogist can tell you the guy’s address” – the potential for false positives is enormous. Police multiply that risk when they run a predicted face through the vast database of facial recognition technology (FRT) algorithms, technology that itself is far from perfect. Despite cautionary language from technology producers and instructions from police departments, many detectives persist in mistakenly believing that FRT returns matches. Instead, it produces possible candidate matches arranged in the order of a “similarity score.” FRT is also better with some types of faces than others. It is up to 100 times more likely to misidentify Asian and Black people than white men. The American Civil Liberties Union, in a thorough 35-page comment to the federal government on FRT, biometric technologies, and predictive algorithms, noted that defects in FRT are likely to multiply when police take a low-quality image and try to brighten it, or reduce pixelation, or otherwise enhance the image. We can only imagine the Frankenstein effect of mating a predicted face with FRT. As PPSA previously reported, rights are violated when police take a facial match not as a clue, but as evidence. This is what happened when Porcha Woodruff, a 32-year-old Black woman and nursing student in Detroit, was arrested on her doorstep while her children cried. Eight months pregnant, she was told by police that she had committed recent carjackings and robberies – even though the woman committing the crimes in the images was not visibly pregnant. Woodruff went into contractions while still in jail. In another case, local police executed a warrant by arresting a Georgia man at his home for a crime committed in Louisiana, even though the arrestee had never set foot in Louisiana. The only explanation for such arrests is sheer laziness, stupidity, or both on the part of the police. As ACLU documents, facial recognition forms warn detectives that a match “should only be considered an investigative lead. Further investigation is needed to confirm a match through other investigative corroborated information and/or evidence. INVESTIGATIVE LEAD, NOT PROBABLE CAUSE TO MAKE AN ARREST.” In the arrests made in Detroit and Georgia, police had not performed any of the rudimentary investigative steps that would have immediately revealed that the person they were investigating was innocent. Carjacking and violent robberies are not typically undertaken by women on the verge of giving birth. The potential for replicating error in the courtroom would be multiplied by showing a predicted face to an eyewitness. If a witness is shown a predicted face, that could easily influence the witness’s memory when presented with a line-up. We understand that an investigation might benefit from knowing that DNA reveals that a perp has blue eyes, allowing investigators to rule out all brown- and green-eyed suspects. But a predicted face should not be enough to search through a database of innocent people. In fact, any searches of facial recognition databases should require a warrant. As technology continues to push the boundaries, states need to develop clear procedural guidelines and warrant requirements that protect constituents’ constitutional rights. Late last year, Sen. Ron Wyden (D-OR) put a hold on the appointment of Lt. Gen. Timothy Haugh to replace outgoing National Security Agency director Gen. Paul Nakasone. Late Thursday, Sen. Wyden’s pressure campaign yielded a stark result – a frank admission from Gen. Nakasone that, as long suspected, the NSA purchases Americans’ sensitive, personal online activities from commercial data brokers.
The NSA admitted it buys netflow data, which records connections between computers and servers. Even without the revelation of messages’ contents, such tracking can be extremely personal. A Stanford University study of telephone metadata showed that a person’s calls and texts can reveal connections to sensitive life issues, from Alcoholics Anonymous to abortion clinics, gun stores, mental and health issues including sexually transmitted disease clinics, and connections to faith organizations. Gen. Nakasone’s letter to Sen. Wyden states that NSA works to minimize the collection of such information. He writes that NSA does not buy location information from phones inside the United States, or purchase the voluminous information collected by our increasingly data-hungry automobiles. It would be a mistake, however, to interpret NSA’s internal restrictions too broadly. While NSA is generally the source for signals intelligence for the other agencies, the FBI, IRS, and the Department of Homeland Security are known to make their own data purchases. In 2020, PPSA reported on the Pentagon purchasing data from Muslim dating and prayer apps. In 2021, Sen. Wyden revealed that the Defense Intelligence Agency was purchasing Americans’ location data from our smartphones without a warrant. How much data, and what kinds of data, are purchased by the FBI is not clear. Sen. Wyden did succeed in a hearing last March in prompting FBI Director Christopher Wray to admit that the FBI had, in some period in the recent past, purchased location data from Americans’ smartphones without a warrant. Despite a U.S. Supreme Court opinion, Carpenter (2018), which held that the U.S. Constitution requires a warrant for the government to compel telecom companies to turn over Americans’ location data, federal agencies maintain that the Carpenter standard does not curb their ability to purchase commercially available digital information. In a press statement, Sen. Wyden hammers home the point that a recent Federal Trade Commission order bans X-Mode Social, a data broker, and its successor company, from selling Americans’ location data to government contractors. Another data broker, InMarket Media, must notify customers before it can sell their precise location data to the government. We now have to ask: was Wednesday’s revelation that the Biden Administration is drafting rules to prevent the sale of Americans’ data to hostile foreign governments an attempt by the administration to partly get ahead of a breaking story? For Americans concerned about privacy, the stakes are high. “Geolocation data can reveal not just where a person lives and whom they spend time with but also, for example, which medical treatments they seek and where they worship,” FTC Chair Lina Khan said in a statement. “The FTC’s action against X-Mode makes clear that businesses do not have free license to market and sell Americans’ sensitive location data. By securing a first-ever ban on the use and sale of sensitive location data, the FTC is continuing its critical work to protect Americans from intrusive data brokers and unchecked corporate surveillance.” As Sen. Wyden’s persistent digging reveals more details about government data purchases, Members of Congress are finding all the more reason to pass the Protect Liberty Act, which enforces the Constitution’s Fourth Amendment warrant requirement when the government inspects Americans’ purchased data. This should also put Members of the Senate and House Intelligence Committees on the spot. They should explain to their colleagues and constituents why they’ve done nothing about government purchases of Americans’ data – and why their bills include exactly nothing to protect Americans’ privacy under the Fourth Amendment. More to come … CVS, Kroger, and Rite Aid Hand Over Americans’ Prescriptions Records to Police Upon Request1/17/2024
Three of the largest pharmaceutical chains – CVS Health, Kroger, and Rite Aid – routinely hand over the prescription and medical records of Americans to police and government agencies upon request, no warrant required.
“Americans' prescription records are among the most private information the government can obtain about a person,” Sen. Ron Wyden (D-OR), and Reps. Pramila Jayapal (D-WA) and Sara Jacobs (D-CA) wrote in a letter to HHS Secretary Xavier Becerra revealing the results of a congressional investigation into this practice. “They can reveal extremely personal and sensitive details about a person’s life, including prescriptions for birth control, depression or anxiety medications, or other private medical conditions.” The Washington Post reports that because the chains often share records across all locations, a pharmacy in one state can access a person’s medical history from states with more restrictive laws. Five pharmacies – Amazon, Cigna, Optum Rx, Walmart, and Walgreens Boots Alliance – require demands for pharmacy records by law enforcement to be reviewed by legal professionals. One of them, Amazon, informs consumers of the request unless hit with a gag order. All the major pharmacies will release customer records, however, if they are merely given a subpoena issued by a government agency rather than a warrant issued by a judge. This could be changed by corporate policy. Sen. Wyden and Reps. Jayapal and Jacobs urge pharmacies to insist on a warrant rather than comply with a request or a subpoena. Most Americans are familiar with the strict privacy provisions of the Health Insurance Portability and Accountability Act (HIPAA) from filling out forms in the doctor’s office. Most will surely be surprised how HIPAA, as strict as it is for physicians and hospitals, is wide open for warrantless inspection by the government. This privacy vulnerability is just one more example of the generous access government agencies have to almost all of our information. Intelligence and law enforcement agencies can know just about everything about us through purchases of our most sensitive and personal information reaped by our apps and sold to the government by data brokers. As privacy champions in Congress press HHS to revise its HIPAA regulations to protect Americans’ medical data from warrantless inspection, Congress should also close all the loopholes by passing the Protect Liberty and End Warrantless Surveillance Act. PPSA has long warned that most drivers don’t realize that a modern car is a digital recording device. It tracks our travels, call logs, private text messages, even the impression our weight makes on our seat. Our car knows if we’re driving alone or with someone else. In all, a contemporary car accumulates vast amounts of data every day, much of it about us, where we’re going, and sometimes with whom.
Kashmir Hill in a recent New York Times piece described how a car can be turned into a digital weapon by a stalker or abusive partner. In one instance, a woman in divorce proceedings realized that her husband was tracking her through the location-based service in her Mercedes. When the woman visited a male friend, her husband sent the man a message with a thumbs-up emoji. Another woman, also estranged from her spouse, found that he was remotely causing her parked Tesla to turn on with heat blasting on hot days, and cold air streaming on cold days. Hill memorably wrote: “A car, to its driver, can feel like a sanctuary. A place to sing favorite songs off key, to cry, to vent or to drive somewhere no one knows you’re going.” That sanctuary, of course, is an illusion. Hill’s piece pointed not just to stalkers, but to the sharing of drivers’ consumer data with insurance companies and car companies. PPSA has long warned of yet another sinister use of car-generated data. About a dozen federal law enforcement and intelligence agencies make free use of the data broker loophole to purchase consumer data scraped from our apps. There is no law or rule that forbids them from purchasing car-generated data as well. This vulnerability will only get worse if a Congressional mandate for a built-in drunk driver detection system leads to cameras and microphones allowing AI to passively monitor drivers’ movements and speech for signs of impairment. Sens. Ron Wyden (D-OR) and Cynthia Lummis (R-WY), and Rep. Ro Khanna (D-CA), have addressed what government can do with car data under proposed legislation, “Closing the Warrantless Digital Car Search Loophole Act.” This bill would require law enforcement to obtain a warrant based on probable cause before searching data from any vehicle that does not require a commercial license. Another similar solution for all purchased commercial data is contained in the Protect Liberty and End Warrantless Surveillance Act, which passed the House Judiciary Committee with overwhelming bipartisan support. The most maddening thing about all this car-generated data is that much of it is off-limits to the drivers themselves, especially if someone else (like an ex-spouse) owns the car’s title. Cars are driving the expectation of privacy off the road. It is time for Congress to act. Less consumer tracking leads to less fraud. That’s the key takeaway from a new study conducted by the National Bureau of Economic Research in its working paper, “Consumer Surveillance and Financial Fraud.”
Using data obtained from the Federal Trade Commission and the Consumer Financial Protection Bureau, as well as the geospatial data firm Safegraph, the authors looked at the correlation between Apple’s App Tracking Transparency framework and consumer fraud reports. Apple’s ATT policy requires user authorization before other apps can track and share customer data. In April 2021, Apple made this the default setting on all iPhones, ensuring that users would no longer be automatically tracked when they visit websites or use apps. This in turn dealt a hefty financial blow to companies like Snap, Facebook, Twitter, and YouTube, which collectively lost about $10 billion after implementation. The authors of the paper obtained fraud complaint figures from the FTC and the CFPB, then employed machine learning and targeted keyword searches to isolate complaints stemming from data privacy issues. They then cross-referenced those complaints with data acquired by Safegraph showing the number of iPhone users in a given ZIP code. According to the paper, a 10% increase in Apple users within a given ZIP code leads to a 3.21% reduction in financial fraud complaints. As the Electronic Frontier Foundation points out in a recent article about the study: “While the scope of the data is small, this is the first significant research we’ve seen that connects increased privacy with decreased fraud. This should matter to all of us. It reinforces that when companies take steps to protect our privacy, they also help protect us from financial fraud.” Obviously, more companies should follow Apple’s lead in implementing ATT-like policies. More than that, however, we need better and more robust laws on the books protecting consumer privacy. California has passed a number of related bills in recent years, most recently creating a one-stop opt-out mechanism for data collection. Colorado did the same. As other states and nations (and even CIA agents) wake up to the dangers of data tracking, this new study can serve as compelling, direct evidence showing why more restrictive settings – and consumer privacy – should always be the default. PPSA has often covered abuses of the geolocation tracking common to cellphones – from local governments in California spying on church-goers, to “warrant factories” in Virginia in which police obtain hundreds of warrants for thousands of surveillance days, often for minor infractions.
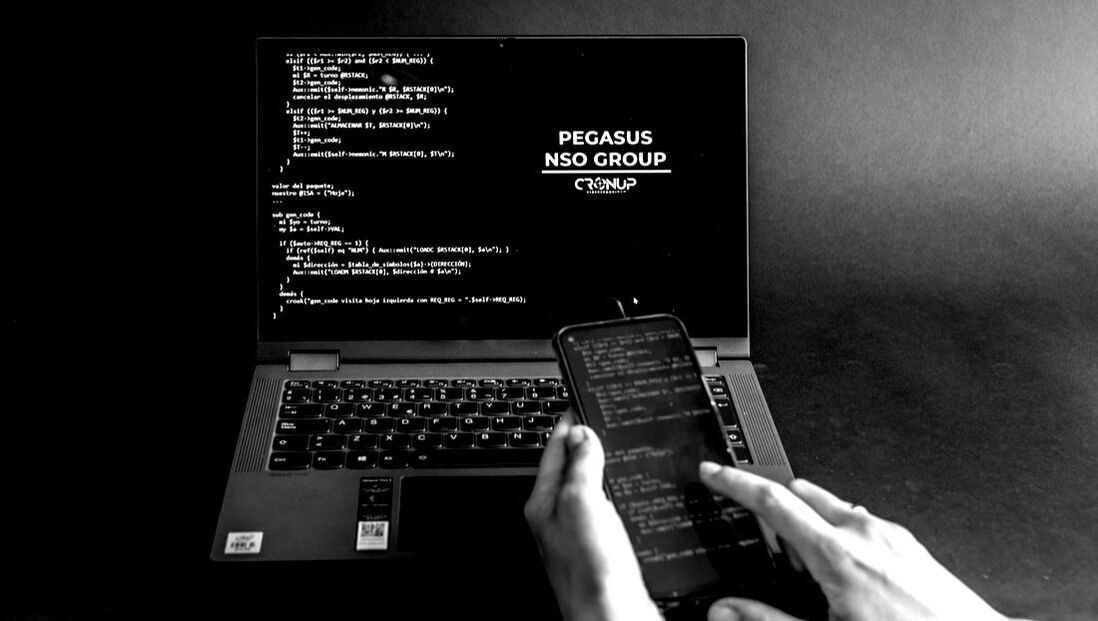
Geolocation tracking can be among the most pernicious compromises of personal privacy. In Carpenter v. United States (2018), the U.S. Supreme Court held that warrants are needed to inspect cellphone records extracted from cell-site towers, recognizing just how personal a target’s movements can be. Writing for the majority, Chief Justice John Roberts wrote: “Unlike the nosy neighbor who keeps an eye on comings and goings, they [new technologies] are ever alert, and memory is nearly infallible.” The narrowness of Carpenter has not, however, prevented the FBI and other federal agencies from tracking people’s movements without a warrant by merely buying their data from third-party data brokers. The FBI may soon, however, have much less to buy. Orin Kerr, writing in the Volokh Conspiracy in Reason, informs us that “Google will no longer keep location history even for the users who opted to have it turned on. Instead, the location history will only be kept on the user’s phones.” Kerr adds: “If Google doesn’t keep the records, Google will have no records to turn over.” A corporate decision in Silicon Valley has thus removed a major pillar of government surveillance. It says something about the current state of this country when a Big Tech giant is more responsive to consumers than government is to its citizens. But don’t be surprised if the feds start to pressure Google to reverse its decision. Will Dream Security Tech Be Marketed More Ethically than Pegasus?According to the Wall Street Journal, Shalev Hulio, former chief executive of NSO Group, the company behind the controversial Pegasus spyware, has launched a new cybersecurity firm in the wake of the Israel-Hamas war. The company, Dream Security, uses artificial intelligence to identify and analyze cyber threats.
So far, the company is already valued at more than $200 million, with customers in Israel and Europe. The need is obvious: European governments and other critical infrastructure have seen increased cyber risks since Russia invaded Ukraine in February 2022. After the recent Hamas raid and atrocities, Israel itself has become a red-hot target. Israel needs and deserves every advantage it can muster in protecting itself. But given the history of NSO and Pegasus, we must raise concern about the risks if Dream Security products were to be sold – as Pegasus was – to irresponsible and dangerous foreign governments and hostile actors. Pegasus has already been implicated in facilitating the murder of journalists and at least one dissident, spying on State Department discussions about an abducted American, and used by politicians in Spain and India against journalists and rivals. Artificial intelligence is a nascent technology. There is no telling how it may yet impact the evolving nature of modern warfare, even if developed for defensive purposes. We support any technology that enhances the security of the Israeli people. But it is in everybody’s best interests that Dream Security commits to only doing business with responsible state and corporate actors. PPSA will be monitoring this story as it develops. Every now and then, even with an outlook jaded by knowledge of the many ways we can be surveilled, we come across some new outrage and find ourselves shouting – “no, wait, they’re doing what?”
The final dismissal of a class-action lawsuit law by a federal judge in Seattle on Tuesday reveals a precise and disturbing way in which our cars are spying on us. Cars hold the contents of our texts messages and phone call records in a way that can be retrieved by the government but not by us. The judge in this case ruled that Honda, Toyota, Volkswagen, and General Motors did not meet the necessary threshold to be held in violation of a Washington State privacy law. The claim was that the onboard entertainment system in these vehicles record and intercept customers’ private text messages and mobile phone call logs. The class-action failed because the Washington Privacy Act’s standard requires a plaintiff to approve that “his or her business, his or her person, or his or her reputation” has been threatened. What emerged from this loss in court is still alarming. Software in cars made by Maryland-based Berla Corp. (slogan: “Staggering Amounts of Data. Endless Possibilities”) allows messages to be downloaded but makes it impossible for vehicle owners to access their communications and call logs. Law enforcement, however, can gain ready access to our data, while car manufacturers make extra money selling our data to advertisers. This brings to mind legislation proposed in 2021 by Sens. Ron Wyden (D-OR) and Cynthia Lummis (R-WY) along with Reps. Peter Meijer (R-MI) and Ro Khanna (D-CA). Under their proposal, law enforcement would have to obtain a warrant based on probable cause before searching data from any vehicle that does not require a commercial driver’s license. Under the “Closing the Warrantless Digital Car Search Loophole Act,” any vehicle data obtained in violation of this law would be inadmissible in court. Sen. Wyden in a statement at the time said: “Americans’ Fourth Amendment rights shouldn’t disappear just because they’ve stepped into a car.” They shouldn’t. But as this federal judge made clear, they do. The Government Surveillance Reform Act (GSRA) Four bipartisan champions of civil liberties – Sen. Ron Wyden (D-OR), Sen. Mike Lee (R-UT), Rep. Warren Davidson (R-OH) and Rep. Zoe Lofgren (D-CA) – today introduced the Government Surveillance Reform Act (GSRA), legislation that restores force to overused Capitol Hill adjectives like “landmark,” “sweeping,” and “comprehensive.”
“The Government Surveillance Reform Act is ambitious in scope, thoughtful in its details, and wide-ranging in its application,” said Bob Goodlatte, former Chairman of the House Judiciary Committee and PPSA’s Senior Policy Advisor. “The GSRA is a once-in-a-generation opportunity for wide-ranging reform.” The GSRA curbs the warrantless surveillance of Americans by federal agencies, while restoring the principles of the Fourth Amendment and the policies that underlie it. The authors of this bill set out to achieve this goal by reforming how the government uses three mechanisms to surveil the American people.
The GSRA will rein in this ballooning surveillance system in many ways.
“The GSRA enjoys widespread bipartisan support because it represents the most balanced and comprehensive surveillance reform bill in 45 years,” Goodlatte said. “PPSA joins with a wide-ranging coalition of civil liberties organizations to urge Congress to make the most of this rare opportunity to put guardrails on federal surveillance of Americans. “We commend Senators Wyden and Lee, and Representatives Davidson and Lofgren, for writing such a thorough and precise bill in the protection of the constitutional rights of every American.” Apple Sends Notice of Hack Pegasus – the Israeli-made spyware – continues to proliferate and enable bad actors to persecute journalists, dissidents, opposition politicians, and crime victims around the world.
This spyware transforms a smartphone into the surveillance equivalent of a Swiss Army knife. Pegasus has a “zero-day” capability, able to infiltrate any Apple or Android phone remotely, without requiring the users to fall for a phishing scam or click on some other trick. Once uploaded, Pegasus turns the victim’s camera and microphone into a 24/7 surveillance device, while also hoovering up every bit of data that passes through the device – from location histories to text, email, and phone messages. We’ve written about how Mexican cartels have used Pegasus to track down and murder journalists. We’ve covered the role of Pegasus in the murder of Saudi dissident Adnan Khashoggi, and how an African government used it to spy on an American woman while she was receiving a briefing inside a State Department facility on her father’s abduction. Now fresh evidence from Apple alerts shows how Pegasus continues to be used by governments to spy on political opponents. Journalists have learned that the Israeli-based NSO Group has sold its spyware to at least 10 governments. Two years ago, it was revealed that a government had used Pegasus to surveil Spanish politicians, including the prime minister, as well as regional politicians. Now it is happening in India. On Oct. 31, just in time for Halloween, Apple sent notices to more than 20 prominent journalists, think tank officials, and politicians in opposition to Prime Minster Narenda Modi that hacking attempts had been made on their smartphones. In 2021, The Washington Post and other media organizations investigated a list obtained by Forbidden Stories, a Paris-based non-profit media outlet, tracking down more than 1,000 phone numbers of hundreds of prominent Indians who were set to be surveilled by Pegasus. This plan now seems to have been executed, at least in part. “Spyware technology has been used to clamp down on human rights and stifle freedom of assembly and expression,” said Likhita Banerj of Amnesty International. “In this atmosphere, the reports of prominent journalists and opposition leaders receiving the Apple notifications are particularly concerning in the months leading up to state and national elections.” Yesterday Spain, today India, tomorrow the United States? It is public knowledge that the FBI owns a copy of Pegasus and that a recent high-level government attorney from the intelligence community has signed on to represent the NSO Group. This is all the more reason for Congress to pass serious reforms to Section 702 of the Foreign Intelligence Surveillance Act, to curtail all forms of illicit government surveillance of Americans. PPSA will continue to monitor this story. |
Categories
All
|



















 RSS Feed
RSS Feed